mirror of
https://github.com/stefanprodan/podinfo.git
synced 2026-04-07 11:36:50 +00:00
Compare commits
104 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
070535aa6d | ||
|
|
33fa95b452 | ||
|
|
b0d5fe73c6 | ||
|
|
f8078c6d9c | ||
|
|
c91289539f | ||
|
|
9e4271c32f | ||
|
|
e107323152 | ||
|
|
a5cb68c49f | ||
|
|
745022dcb3 | ||
|
|
7c88a31f52 | ||
|
|
89cd76ceca | ||
|
|
344813ab4c | ||
|
|
ad9cc3d42c | ||
|
|
71bc8b76ec | ||
|
|
67fc5cf534 | ||
|
|
46d18e955a | ||
|
|
1e40803bfb | ||
|
|
13f116b808 | ||
|
|
ccdea85f0a | ||
|
|
095bfb37f3 | ||
|
|
9e6a339fef | ||
|
|
a1b2bc79b8 | ||
|
|
37522319db | ||
|
|
e4a96f95c8 | ||
|
|
a888f4d135 | ||
|
|
d2bfab977c | ||
|
|
e4b5093912 | ||
|
|
a9565e1b27 | ||
|
|
40bbbc12b3 | ||
|
|
f349616a3f | ||
|
|
3cb08bab98 | ||
|
|
fd63e6ef74 | ||
|
|
d9e61b07cc | ||
|
|
7ddb9ea518 | ||
|
|
41ec5f60fb | ||
|
|
8613002a6f | ||
|
|
6f98421d8b | ||
|
|
9c36d89171 | ||
|
|
53c814115d | ||
|
|
7a2877f879 | ||
|
|
2a8de2bbca | ||
|
|
be7f93c668 | ||
|
|
b33567f025 | ||
|
|
2451f71581 | ||
|
|
50d9e3e07c | ||
|
|
7601e8e35b | ||
|
|
b541f90a3d | ||
|
|
275c8ffaf6 | ||
|
|
44fd560f3b | ||
|
|
c86e56a991 | ||
|
|
f04a6ec789 | ||
|
|
a68db07056 | ||
|
|
b15f8fe4ab | ||
|
|
292d4e77fd | ||
|
|
dde1a73968 | ||
|
|
52ca29260c | ||
|
|
45da3ab58d | ||
|
|
e1972b7afc | ||
|
|
a120ff1cc4 | ||
|
|
545edabf5c | ||
|
|
2589634047 | ||
|
|
d439dc2edf | ||
|
|
62546e0a69 | ||
|
|
80f46daa4a | ||
|
|
b8bc6f76e4 | ||
|
|
4ed0f6030e | ||
|
|
9653561ccf | ||
|
|
3a2e56dc7d | ||
|
|
955410a94c | ||
|
|
021401fd43 | ||
|
|
a9f6446865 | ||
|
|
803456eddd | ||
|
|
2a7425f6e2 | ||
|
|
b51d46649a | ||
|
|
34a2b2a571 | ||
|
|
d89cf7db10 | ||
|
|
80d5183749 | ||
|
|
2651dae114 | ||
|
|
5a68383db6 | ||
|
|
e4c3b94f0a | ||
|
|
c1689ad24a | ||
|
|
a3ae18b304 | ||
|
|
a7be119f20 | ||
|
|
c59466012f | ||
|
|
cd7ad53eae | ||
|
|
25fff58ba5 | ||
|
|
d1001f0eb5 | ||
|
|
0fe07bef97 | ||
|
|
a044694622 | ||
|
|
efe5de74c0 | ||
|
|
8aa52e8afd | ||
|
|
874791526a | ||
|
|
037eaa9d63 | ||
|
|
5920bfdbe3 | ||
|
|
d298670b09 | ||
|
|
5a05ae2f98 | ||
|
|
0fe3652b5b | ||
|
|
c60a8f7fee | ||
|
|
0b7676a2db | ||
|
|
0ed8c210c1 | ||
|
|
f1fe3f3d2b | ||
|
|
52b5958a86 | ||
|
|
90af761766 | ||
|
|
3dc9ac574e |
5
.circleci/config.yml
Normal file
5
.circleci/config.yml
Normal file
@@ -0,0 +1,5 @@
|
||||
version: 2
|
||||
jobs:
|
||||
build:
|
||||
branches:
|
||||
ignore: gh-pages
|
||||
@@ -1,61 +0,0 @@
|
||||
# Podinfo signed releases
|
||||
|
||||
Podinfo release assets (container image, Helm chart, Flux artifact, Timoni module)
|
||||
are published to GitHub Container Registry and are signed with
|
||||
[Cosign v2](https://github.com/sigstore/cosign) keyless & GitHub Actions OIDC.
|
||||
|
||||
## Verify podinfo with cosign
|
||||
|
||||
Install the [cosign](https://github.com/sigstore/cosign) CLI:
|
||||
|
||||
```sh
|
||||
brew install sigstore/tap/cosign
|
||||
```
|
||||
|
||||
### Container image
|
||||
|
||||
Verify the podinfo container image hosted on GHCR:
|
||||
|
||||
```sh
|
||||
cosign verify ghcr.io/stefanprodan/podinfo:6.5.0 \
|
||||
--certificate-identity-regexp="^https://github.com/stefanprodan/podinfo.*$" \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com
|
||||
```
|
||||
|
||||
Verify the podinfo container image hosted on Docker Hub:
|
||||
|
||||
```sh
|
||||
cosign verify docker.io/stefanprodan/podinfo:6.5.0 \
|
||||
--certificate-identity-regexp="^https://github.com/stefanprodan/podinfo.*$" \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com
|
||||
```
|
||||
|
||||
### Helm chart
|
||||
|
||||
Verify the podinfo [Helm](https://helm.sh) chart hosted on GHCR:
|
||||
|
||||
```sh
|
||||
cosign verify ghcr.io/stefanprodan/charts/podinfo:6.5.0 \
|
||||
--certificate-identity-regexp="^https://github.com/stefanprodan/podinfo.*$" \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com
|
||||
```
|
||||
|
||||
### Flux artifact
|
||||
|
||||
Verify the podinfo [Flux](https://fluxcd.io) artifact hosted on GHCR:
|
||||
|
||||
```sh
|
||||
cosign verify ghcr.io/stefanprodan/manifests/podinfo:6.5.0 \
|
||||
--certificate-identity-regexp="^https://github.com/stefanprodan/podinfo.*$" \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com
|
||||
```
|
||||
|
||||
### Timoni module
|
||||
|
||||
Verify the podinfo [Timoni](https://timoni.sh) module hosted on GHCR:
|
||||
|
||||
```sh
|
||||
cosign verify ghcr.io/stefanprodan/modules/podinfo:6.5.0 \
|
||||
--certificate-identity-regexp="^https://github.com/stefanprodan/podinfo.*$" \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com
|
||||
```
|
||||
@@ -1,4 +0,0 @@
|
||||
-----BEGIN PUBLIC KEY-----
|
||||
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAEST+BqQ1XZhhVYx0YWQjdUJYIG5Lt
|
||||
iz2+UxRIqmKBqNmce2T+l45qyqOs99qfD7gLNGmkVZ4vtJ9bM7FxChFczg==
|
||||
-----END PUBLIC KEY-----
|
||||
1
.gitattributes
vendored
1
.gitattributes
vendored
@@ -1 +0,0 @@
|
||||
timoni/podinfo/cue.mod/** linguist-vendored
|
||||
1
.github/FUNDING.yml
vendored
1
.github/FUNDING.yml
vendored
@@ -1 +0,0 @@
|
||||
github: stefanprodan
|
||||
38
.github/actions/kubeconform/action.yml
vendored
38
.github/actions/kubeconform/action.yml
vendored
@@ -1,38 +0,0 @@
|
||||
name: Setup kubeconform
|
||||
description: A GitHub Action for running kubeconform commands
|
||||
author: Stefan Prodan
|
||||
branding:
|
||||
color: blue
|
||||
icon: command
|
||||
inputs:
|
||||
version:
|
||||
description: "kubeconform version e.g. 0.5.0 (defaults to latest stable release)"
|
||||
required: false
|
||||
arch:
|
||||
description: "arch can be amd64 or arm64"
|
||||
required: true
|
||||
default: "amd64"
|
||||
runs:
|
||||
using: composite
|
||||
steps:
|
||||
- name: "Download binary to the GH runner cache"
|
||||
shell: bash
|
||||
run: |
|
||||
ARCH=${{ inputs.arch }}
|
||||
VERSION=${{ inputs.version }}
|
||||
|
||||
if [ -z $VERSION ]; then
|
||||
VERSION=$(curl https://api.github.com/repos/yannh/kubeconform/releases/latest -sL | grep tag_name | sed -E 's/.*"([^"]+)".*/\1/' | cut -c 2-)
|
||||
fi
|
||||
|
||||
BIN_URL="https://github.com/yannh/kubeconform/releases/download/v${VERSION}/kubeconform-linux-${ARCH}.tar.gz"
|
||||
BIN_DIR=$RUNNER_TOOL_CACHE/kubeconform/$VERSION/$ARCH
|
||||
|
||||
if [[ ! -x "$BIN_DIR/kind" ]]; then
|
||||
mkdir -p $BIN_DIR
|
||||
cd $BIN_DIR
|
||||
curl -sL $BIN_URL | tar xz
|
||||
chmod +x kubeconform
|
||||
fi
|
||||
|
||||
echo "$BIN_DIR" >> "$GITHUB_PATH"
|
||||
24
.github/actions/runner-cleanup/action.yml
vendored
24
.github/actions/runner-cleanup/action.yml
vendored
@@ -1,24 +0,0 @@
|
||||
name: Runner Cleanup
|
||||
description: A GitHub Action for removing bloat from Ubuntu GitHub Actions runner.
|
||||
author: Stefan Prodan
|
||||
branding:
|
||||
color: blue
|
||||
icon: command
|
||||
runs:
|
||||
using: composite
|
||||
steps:
|
||||
- name: "Disk Usage Before Cleanup"
|
||||
shell: bash
|
||||
run: |
|
||||
df -h
|
||||
- name: "Remove .NET, Android and Haskell"
|
||||
shell: bash
|
||||
run: |
|
||||
sudo rm -rf /usr/share/dotnet || true
|
||||
sudo rm -rf /usr/local/lib/android || true
|
||||
sudo rm -rf /opt/ghc || true
|
||||
sudo rm -rf /usr/local/.ghcup || true
|
||||
- name: "Disk Usage After Cleanup"
|
||||
shell: bash
|
||||
run: |
|
||||
df -h
|
||||
11
.github/dependabot.yaml
vendored
11
.github/dependabot.yaml
vendored
@@ -1,11 +0,0 @@
|
||||
version: 2
|
||||
|
||||
updates:
|
||||
- package-ecosystem: "github-actions"
|
||||
directory: "/"
|
||||
groups:
|
||||
actions:
|
||||
patterns:
|
||||
- "*"
|
||||
schedule:
|
||||
interval: "weekly"
|
||||
25
.github/workflows/cve-scan.yml
vendored
25
.github/workflows/cve-scan.yml
vendored
@@ -1,25 +0,0 @@
|
||||
name: cve-scan
|
||||
|
||||
on:
|
||||
workflow_dispatch:
|
||||
push:
|
||||
branches:
|
||||
- "master"
|
||||
pull_request:
|
||||
branches:
|
||||
- "master"
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
govulncheck:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- uses: actions/checkout@v6
|
||||
- uses: ./.github/actions/runner-cleanup
|
||||
- name: Vulnerability scan
|
||||
id: govulncheck
|
||||
uses: golang/govulncheck-action@v1
|
||||
with:
|
||||
repo-checkout: false
|
||||
80
.github/workflows/e2e.yml
vendored
80
.github/workflows/e2e.yml
vendored
@@ -1,80 +0,0 @@
|
||||
name: e2e
|
||||
|
||||
on:
|
||||
pull_request:
|
||||
push:
|
||||
branches:
|
||||
- 'master'
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
kind-helm:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v6
|
||||
- name: Disk Cleanup
|
||||
uses: ./.github/actions/runner-cleanup
|
||||
- name: Setup Kubernetes
|
||||
uses: helm/kind-action@v1.14.0
|
||||
with:
|
||||
cluster_name: kind
|
||||
- name: Build container image
|
||||
run: |
|
||||
./test/build.sh
|
||||
kind load docker-image test/podinfo:latest
|
||||
- name: Setup Helm
|
||||
uses: azure/setup-helm@v4
|
||||
with:
|
||||
version: v4.1.0
|
||||
- name: Deploy
|
||||
run: ./test/deploy.sh
|
||||
- name: Run integration tests
|
||||
run: ./test/test.sh
|
||||
- name: Debug failure
|
||||
if: failure()
|
||||
run: |
|
||||
kubectl logs -l app=podinfo || true
|
||||
kind-timoni:
|
||||
runs-on: ubuntu-latest
|
||||
services:
|
||||
registry:
|
||||
image: registry:2
|
||||
ports:
|
||||
- 5000:5000
|
||||
env:
|
||||
PODINFO_IMAGE_URL: "test/podinfo"
|
||||
PODINFO_MODULE_URL: "oci://localhost:5000/podinfo"
|
||||
PODINFO_VERSION: "0.0.0-devel"
|
||||
steps:
|
||||
- uses: actions/checkout@v6
|
||||
- uses: ./.github/actions/runner-cleanup
|
||||
- name: Setup Timoni
|
||||
uses: stefanprodan/timoni/actions/setup@main
|
||||
- name: Setup Kubernetes
|
||||
uses: helm/kind-action@v1.14.0
|
||||
with:
|
||||
cluster_name: kind
|
||||
- name: Build container
|
||||
run: |
|
||||
docker build -t ${PODINFO_IMAGE_URL}:${PODINFO_VERSION} --build-arg "REVISION=${GITHUB_SHA}" -f Dockerfile.xx .
|
||||
kind load docker-image ${PODINFO_IMAGE_URL}:${PODINFO_VERSION}
|
||||
- name: Vet module
|
||||
run: |
|
||||
timoni mod vet ./timoni/podinfo --debug
|
||||
- name: Build module
|
||||
run: |
|
||||
timoni mod push ./timoni/podinfo ${PODINFO_MODULE_URL} -v ${PODINFO_VERSION}
|
||||
- name: Apply bundle
|
||||
run: |
|
||||
timoni bundle apply -f ./timoni/bundles/test.podinfo.cue --runtime-from-env
|
||||
- name: Verify status
|
||||
run: |
|
||||
timoni -n podinfo status backend
|
||||
timoni -n podinfo status frontend
|
||||
- name: Debug failure
|
||||
if: failure()
|
||||
run: |
|
||||
kubectl -n podinfo get all || true
|
||||
166
.github/workflows/release.yml
vendored
166
.github/workflows/release.yml
vendored
@@ -1,166 +0,0 @@
|
||||
name: release
|
||||
|
||||
on:
|
||||
push:
|
||||
tags:
|
||||
- '*'
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
jobs:
|
||||
release:
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
contents: write # needed to write releases
|
||||
id-token: write # needed for keyless signing
|
||||
packages: write # needed for ghcr access
|
||||
steps:
|
||||
- uses: actions/checkout@v6
|
||||
- uses: ./.github/actions/runner-cleanup
|
||||
- uses: sigstore/cosign-installer@v4.0.0
|
||||
- uses: fluxcd/flux2/action@v2.8.1
|
||||
- uses: stefanprodan/timoni/actions/setup@v0.26.0
|
||||
- name: Setup Notation CLI
|
||||
uses: notaryproject/notation-action/setup@v1
|
||||
with:
|
||||
version: "1.1.0"
|
||||
- name: Setup Notation signing keys
|
||||
run: |
|
||||
mkdir -p ~/.config/notation/localkeys/
|
||||
cp ./.notation/signingkeys.json ~/.config/notation/
|
||||
cp ./.notation/notation.crt ~/.config/notation/localkeys/
|
||||
echo "$NOTATION_KEY" > ~/.config/notation/localkeys/notation.key
|
||||
env:
|
||||
NOTATION_KEY: ${{ secrets.NOTATION_SIGNING_KEY }}
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@v6
|
||||
with:
|
||||
go-version: 1.26.x
|
||||
- name: Setup Helm
|
||||
uses: azure/setup-helm@v4
|
||||
with:
|
||||
version: v4.1.1
|
||||
- name: Setup QEMU
|
||||
uses: docker/setup-qemu-action@v3
|
||||
with:
|
||||
platforms: all
|
||||
- name: Setup Docker Buildx
|
||||
id: buildx
|
||||
uses: docker/setup-buildx-action@v3
|
||||
- name: Login to GitHub Container Registry
|
||||
uses: docker/login-action@v3
|
||||
with:
|
||||
registry: ghcr.io
|
||||
username: ${{ github.actor }}
|
||||
password: ${{ secrets.GITHUB_TOKEN }}
|
||||
- name: Login to Docker Hub
|
||||
uses: docker/login-action@v3
|
||||
with:
|
||||
username: ${{ secrets.DOCKER_USERNAME }}
|
||||
password: ${{ secrets.DOCKER_PASSWORD }}
|
||||
- name: Prepare
|
||||
id: prep
|
||||
run: |
|
||||
VERSION=sha-${GITHUB_SHA::8}
|
||||
if [[ $GITHUB_REF == refs/tags/* ]]; then
|
||||
VERSION=${GITHUB_REF/refs\/tags\//}
|
||||
fi
|
||||
echo "BUILD_DATE=$(date -u +'%Y-%m-%dT%H:%M:%SZ')" >> $GITHUB_OUTPUT
|
||||
echo "VERSION=${VERSION}" >> $GITHUB_OUTPUT
|
||||
echo "REVISION=${GITHUB_SHA}" >> $GITHUB_OUTPUT
|
||||
- name: Generate images meta
|
||||
id: meta
|
||||
uses: docker/metadata-action@v5
|
||||
with:
|
||||
images: |
|
||||
docker.io/stefanprodan/podinfo
|
||||
ghcr.io/stefanprodan/podinfo
|
||||
tags: |
|
||||
type=raw,value=${{ steps.prep.outputs.VERSION }}
|
||||
type=raw,value=latest
|
||||
- name: Publish multi-arch image
|
||||
uses: docker/build-push-action@v6
|
||||
with:
|
||||
sbom: true
|
||||
provenance: true
|
||||
push: true
|
||||
builder: ${{ steps.buildx.outputs.name }}
|
||||
context: .
|
||||
file: ./Dockerfile.xx
|
||||
build-args: |
|
||||
REVISION=${{ steps.prep.outputs.REVISION }}
|
||||
platforms: linux/amd64,linux/arm/v7,linux/arm64
|
||||
tags: ${{ steps.meta.outputs.tags }}
|
||||
labels: ${{ steps.meta.outputs.labels }}
|
||||
- name: Publish Timoni module to GHCR
|
||||
run: |
|
||||
timoni mod push ./timoni/podinfo oci://ghcr.io/stefanprodan/modules/podinfo \
|
||||
--sign cosign \
|
||||
--version ${{ steps.prep.outputs.VERSION }} \
|
||||
-a 'org.opencontainers.image.source=https://github.com/stefanprodan/podinfo' \
|
||||
-a 'org.opencontainers.image.licenses=Apache-2.0' \
|
||||
-a 'org.opencontainers.image.description=A timoni.sh module for deploying Podinfo.' \
|
||||
-a 'org.opencontainers.image.documentation=https://github.com/stefanprodan/podinfo/blob/main/timoni/podinfo/README.md'
|
||||
- name: Publish Helm chart to GHCR
|
||||
run: |
|
||||
helm package charts/podinfo
|
||||
helm push podinfo-${{ steps.prep.outputs.VERSION }}.tgz oci://ghcr.io/stefanprodan/charts
|
||||
rm podinfo-${{ steps.prep.outputs.VERSION }}.tgz
|
||||
- name: Publish Flux OCI artifact to GHCR
|
||||
run: |
|
||||
flux push artifact oci://ghcr.io/stefanprodan/manifests/podinfo:${{ steps.prep.outputs.VERSION }} \
|
||||
--path="./kustomize" \
|
||||
--source="${{ github.event.repository.html_url }}" \
|
||||
--revision="${GITHUB_REF_NAME}/${GITHUB_SHA}"
|
||||
flux tag artifact oci://ghcr.io/stefanprodan/manifests/podinfo:${{ steps.prep.outputs.VERSION }} --tag latest
|
||||
- name: Sign artifacts with Cosign
|
||||
env:
|
||||
COSIGN_EXPERIMENTAL: 1
|
||||
run: |
|
||||
cosign sign docker.io/stefanprodan/podinfo:${{ steps.prep.outputs.VERSION }} --yes
|
||||
cosign sign ghcr.io/stefanprodan/podinfo:${{ steps.prep.outputs.VERSION }} --yes
|
||||
cosign sign ghcr.io/stefanprodan/charts/podinfo:${{ steps.prep.outputs.VERSION }} --yes
|
||||
cosign sign ghcr.io/stefanprodan/manifests/podinfo:${{ steps.prep.outputs.VERSION }} --yes
|
||||
- name: Publish base image
|
||||
uses: docker/build-push-action@v6
|
||||
with:
|
||||
push: true
|
||||
builder: ${{ steps.buildx.outputs.name }}
|
||||
context: .
|
||||
platforms: linux/amd64
|
||||
file: ./Dockerfile.base
|
||||
tags: docker.io/stefanprodan/podinfo-base:latest
|
||||
- name: Publish helm chart
|
||||
uses: stefanprodan/helm-gh-pages@master
|
||||
with:
|
||||
token: ${{ secrets.GITHUB_TOKEN }}
|
||||
- name: Publish config artifact
|
||||
run: |
|
||||
flux push artifact oci://ghcr.io/stefanprodan/podinfo-deploy:${{ steps.prep.outputs.VERSION }} \
|
||||
--path="./kustomize" \
|
||||
--source="${{ github.event.repository.html_url }}" \
|
||||
--revision="${GITHUB_REF_NAME}/${GITHUB_SHA}"
|
||||
flux tag artifact oci://ghcr.io/stefanprodan/podinfo-deploy:${{ steps.prep.outputs.VERSION }} --tag latest
|
||||
- name: Sign config artifact with cso
|
||||
run: |
|
||||
echo "$COSIGN_KEY" > /tmp/cosign.key
|
||||
cosign sign -key /tmp/cosign.key ghcr.io/stefanprodan/podinfo-deploy:${{ steps.prep.outputs.VERSION }} --yes
|
||||
cosign sign -key /tmp/cosign.key ghcr.io/stefanprodan/podinfo-deploy:latest --yes
|
||||
env:
|
||||
COSIGN_PASSWORD: ${{secrets.COSIGN_PASSWORD}}
|
||||
COSIGN_KEY: ${{secrets.COSIGN_KEY}}
|
||||
- name: Sign artifacts with Notation
|
||||
run: |
|
||||
notation sign --signature-format cose ghcr.io/stefanprodan/podinfo:${{ steps.prep.outputs.VERSION }}
|
||||
notation sign --signature-format cose ghcr.io/stefanprodan/charts/podinfo:${{ steps.prep.outputs.VERSION }}
|
||||
notation sign --signature-format cose ghcr.io/stefanprodan/manifests/podinfo:${{ steps.prep.outputs.VERSION }}
|
||||
notation sign --signature-format cose ghcr.io/stefanprodan/podinfo-deploy:${{ steps.prep.outputs.VERSION }}
|
||||
notation sign --signature-format cose ghcr.io/stefanprodan/podinfo-deploy:latest
|
||||
- name: Publish release
|
||||
uses: goreleaser/goreleaser-action@v7
|
||||
with:
|
||||
version: latest
|
||||
args: release --skip=validate
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
73
.github/workflows/test.yml
vendored
73
.github/workflows/test.yml
vendored
@@ -1,73 +0,0 @@
|
||||
name: test
|
||||
|
||||
on:
|
||||
pull_request:
|
||||
push:
|
||||
branches:
|
||||
- 'master'
|
||||
|
||||
permissions:
|
||||
contents: read
|
||||
|
||||
env:
|
||||
KUBERNETES_VERSION: 1.35.0
|
||||
HELM_VERSION: 4.1.1
|
||||
|
||||
jobs:
|
||||
test:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- uses: actions/checkout@v6
|
||||
- uses: ./.github/actions/runner-cleanup
|
||||
- name: Setup Go
|
||||
uses: actions/setup-go@v6
|
||||
with:
|
||||
go-version: 1.26.x
|
||||
cache-dependency-path: |
|
||||
**/go.sum
|
||||
**/go.mod
|
||||
- name: Setup kubectl
|
||||
uses: azure/setup-kubectl@v4
|
||||
with:
|
||||
version: v${{ env.KUBERNETES_VERSION }}
|
||||
- name: Setup kubeconform
|
||||
uses: ./.github/actions/kubeconform
|
||||
- name: Setup Helm
|
||||
uses: azure/setup-helm@v4
|
||||
with:
|
||||
version: v${{ env.HELM_VERSION }}
|
||||
- name: Setup CUE
|
||||
uses: cue-lang/setup-cue@v1.0.1
|
||||
- name: Setup Timoni
|
||||
uses: stefanprodan/timoni/actions/setup@v0.26.0
|
||||
- name: Run unit tests
|
||||
run: make test
|
||||
- name: Validate Helm chart
|
||||
run: |
|
||||
helm lint ./charts/podinfo/
|
||||
helm template ./charts/podinfo/ | kubeconform -strict -summary -kubernetes-version ${{ env.KUBERNETES_VERSION }}
|
||||
- name: Validate Kustomize overlay
|
||||
run: |
|
||||
kubectl kustomize ./kustomize/ | kubeconform -strict -summary -kubernetes-version ${{ env.KUBERNETES_VERSION }}
|
||||
- name: Verify CUE formatting
|
||||
working-directory: ./timoni/podinfo
|
||||
run: |
|
||||
cue fmt ./...
|
||||
status=$(git status . --porcelain)
|
||||
[[ -z "$status" ]] || {
|
||||
echo "CUE files are not correctly formatted"
|
||||
echo "$status"
|
||||
git diff
|
||||
exit 1
|
||||
}
|
||||
- name: Validate Timoni module
|
||||
working-directory: ./timoni/podinfo
|
||||
run: |
|
||||
timoni mod lint .
|
||||
timoni build podinfo . -f test_values.cue | kubeconform -strict -summary -skip=ServiceMonitor -kubernetes-version ${{ env.KUBERNETES_VERSION }}
|
||||
- name: Check if working tree is dirty
|
||||
run: |
|
||||
if [[ $(git diff --stat) != '' ]]; then
|
||||
echo 'run make test and commit changes'
|
||||
exit 1
|
||||
fi
|
||||
28
.gitignore
vendored
28
.gitignore
vendored
@@ -1,28 +0,0 @@
|
||||
# Binaries for programs and plugins
|
||||
*.exe
|
||||
*.dll
|
||||
*.so
|
||||
*.dylib
|
||||
|
||||
# Test binary, build with `go test -c`
|
||||
*.test
|
||||
|
||||
# Output of the go coverage tool, specifically when used with LiteIDE
|
||||
*.out
|
||||
|
||||
.DS_Store
|
||||
|
||||
# Project-local glide cache, RE: https://github.com/Masterminds/glide/issues/736
|
||||
.glide/
|
||||
.idea/
|
||||
release/
|
||||
build/
|
||||
gcloud/
|
||||
dist/
|
||||
bin/
|
||||
cue/cue.mod/gen/
|
||||
cue/go.mod
|
||||
cue/go.sum
|
||||
|
||||
.notation/podinfo.csr
|
||||
.notation/podinfo.key
|
||||
@@ -1,35 +0,0 @@
|
||||
version: 2
|
||||
|
||||
# xref: https://goreleaser.com/customization/project/
|
||||
project_name: podinfo
|
||||
|
||||
# xref: https://goreleaser.com/customization/hooks/
|
||||
before:
|
||||
hooks:
|
||||
- go mod download
|
||||
|
||||
# xref: https://goreleaser.com/customization/env/
|
||||
env:
|
||||
- CGO_ENABLED=0
|
||||
|
||||
# xref: https://goreleaser.com/customization/build/
|
||||
builds:
|
||||
- main: ./cmd/podcli
|
||||
binary: podcli
|
||||
ldflags: -s -w -X github.com/stefanprodan/podinfo/pkg/version.REVISION={{.Commit}}
|
||||
goos:
|
||||
- windows
|
||||
- darwin
|
||||
- linux
|
||||
goarch:
|
||||
- amd64
|
||||
|
||||
# xref: https://goreleaser.com/customization/archive/
|
||||
archives:
|
||||
- name_template: "{{ .Binary }}_{{ .Version }}_{{ .Os }}_{{ .Arch }}"
|
||||
files:
|
||||
- LICENSE
|
||||
|
||||
# xref: https://goreleaser.com/customization/changelog/
|
||||
changelog:
|
||||
use: github-native
|
||||
@@ -1,15 +0,0 @@
|
||||
# Podinfo signed releases
|
||||
|
||||
Podinfo release assets such as the Helm chart and the Flux artifact
|
||||
are published to GitHub Container Registry and are signed with
|
||||
[Notation](https://github.com/notaryproject/notation).
|
||||
|
||||
## Generate signing keys
|
||||
|
||||
Generate a new signing key pair:
|
||||
|
||||
```sh
|
||||
openssl genrsa -out podinfo.key 2048
|
||||
openssl req -new -key podinfo.key -out podinfo.csr -config codesign.cnf
|
||||
openssl x509 -req -days 1826 -in podinfo.csr -signkey podinfo.key -out notation.crt -extensions v3_req -extfile codesign.cnf
|
||||
```
|
||||
@@ -1,18 +0,0 @@
|
||||
[ req ]
|
||||
default_bits = 2048
|
||||
default_keyfile = privatekey.pem
|
||||
distinguished_name = req_distinguished_name
|
||||
req_extensions = v3_req
|
||||
prompt = no
|
||||
|
||||
[ req_distinguished_name ]
|
||||
C = RO
|
||||
ST = BU
|
||||
L = Bucharest
|
||||
O = Notary
|
||||
CN = stefanprodan.com
|
||||
|
||||
[ v3_req ]
|
||||
keyUsage = critical,digitalSignature
|
||||
extendedKeyUsage = critical,codeSigning
|
||||
#subjectKeyIdentifier = hash
|
||||
@@ -1,21 +0,0 @@
|
||||
-----BEGIN CERTIFICATE-----
|
||||
MIIDbDCCAlSgAwIBAgIUP7zhmTw5XTWLcgBGkBEsErMOkz4wDQYJKoZIhvcNAQEL
|
||||
BQAwWjELMAkGA1UEBhMCUk8xCzAJBgNVBAgMAkJVMRIwEAYDVQQHDAlCdWNoYXJl
|
||||
c3QxDzANBgNVBAoMBk5vdGFyeTEZMBcGA1UEAwwQc3RlZmFucHJvZGFuLmNvbTAe
|
||||
Fw0yNDAyMjUxMDAyMzZaFw0yOTAyMjQxMDAyMzZaMFoxCzAJBgNVBAYTAlJPMQsw
|
||||
CQYDVQQIDAJCVTESMBAGA1UEBwwJQnVjaGFyZXN0MQ8wDQYDVQQKDAZOb3Rhcnkx
|
||||
GTAXBgNVBAMMEHN0ZWZhbnByb2Rhbi5jb20wggEiMA0GCSqGSIb3DQEBAQUAA4IB
|
||||
DwAwggEKAoIBAQDtH4oPi3SyX/DGv6NdjIvmApvD9eeSgsmHdwpAly8T9D2me+fx
|
||||
Z+wRNJmq4aq/A1anX+Sg28iwHzV+1WKpsHnjYzDAJSEYP2S8A5H1nGRKUoibdijw
|
||||
C3QBh5C75rjF/tmZVSX/Vgbf3HJJEsF4WUxWabLxoV2QLo7UlEsQd9+bSeKNMncx
|
||||
1+E6FdbRCrYo90iobvZJ8K/S2zCWq/JTeHfTnmSEDhx6nMJcaSjvMPn3zyauWcQw
|
||||
dDpkcaGiJ64fEJRT2OFxXv9u+vDmIMKzo/Wjbd+IzFj6YY4VisK88aU7tmDelnk5
|
||||
gQB9eu62PFoaVsYJp4VOhblFKvGJpQwbWB9BAgMBAAGjKjAoMA4GA1UdDwEB/wQE
|
||||
AwIHgDAWBgNVHSUBAf8EDDAKBggrBgEFBQcDAzANBgkqhkiG9w0BAQsFAAOCAQEA
|
||||
6x+C6hAIbLwMvkNx4K5p7Qe/pLQR0VwQFAw10yr/5KSN+YKFpon6pQ0TebL7qll+
|
||||
uBGZvtQhN6v+DlnVqB7lvJKd+89isgirkkews5KwuXg7Gv5UPIugH0dXISZU8DMJ
|
||||
7J4oKREv5HzdFmfsUfNlQcfyVTjKL6UINXfKGdqNNxXxR9b4a1TY2JcmEhzBTHaq
|
||||
ZqX6HK784a0dB7aHgeFrFwPCCP4M684Hs7CFbk3jo2Ef4ljnB5AyWpe8pwCLMdRt
|
||||
UjSjL5xJWVQvRU+STQsPr6SvpokPCG4rLQyjgeYYk4CCj5piSxbSUZFavq8v1y7Y
|
||||
m91USVqfeUX7ZzjDxPHE2A==
|
||||
-----END CERTIFICATE-----
|
||||
@@ -1,10 +0,0 @@
|
||||
{
|
||||
"default": "stefanprodan.com",
|
||||
"keys": [
|
||||
{
|
||||
"name": "stefanprodan.com",
|
||||
"keyPath": "/home/runner/.config/notation/localkeys/notation.key",
|
||||
"certPath": "/home/runner/.config/notation/localkeys/notation.crt"
|
||||
}
|
||||
]
|
||||
}
|
||||
@@ -1,19 +0,0 @@
|
||||
{
|
||||
"version": "1.0",
|
||||
"trustPolicies": [
|
||||
{
|
||||
"name": "stefanprodan.com",
|
||||
"registryScopes": [
|
||||
"ghcr.io/stefanprodan/podinfo-deploy",
|
||||
"ghcr.io/stefanprodan/charts/podinfo"
|
||||
],
|
||||
"signatureVerification": {
|
||||
"level" : "strict"
|
||||
},
|
||||
"trustStores": [ "ca:stefanprodan.com" ],
|
||||
"trustedIdentities": [
|
||||
"x509.subject: C=RO, ST=BU, L=Bucharest, O=Notary, CN=stefanprodan.com"
|
||||
]
|
||||
}
|
||||
]
|
||||
}
|
||||
43
Dockerfile
43
Dockerfile
@@ -1,43 +0,0 @@
|
||||
FROM golang:1.26-alpine AS builder
|
||||
|
||||
ARG REVISION
|
||||
|
||||
RUN mkdir -p /podinfo/
|
||||
|
||||
WORKDIR /podinfo
|
||||
|
||||
COPY . .
|
||||
|
||||
RUN go mod download
|
||||
|
||||
RUN CGO_ENABLED=0 go build -ldflags "-s -w \
|
||||
-X github.com/stefanprodan/podinfo/pkg/version.REVISION=${REVISION}" \
|
||||
-a -o bin/podinfo cmd/podinfo/*
|
||||
|
||||
RUN CGO_ENABLED=0 go build -ldflags "-s -w \
|
||||
-X github.com/stefanprodan/podinfo/pkg/version.REVISION=${REVISION}" \
|
||||
-a -o bin/podcli cmd/podcli/*
|
||||
|
||||
FROM alpine:3.23
|
||||
|
||||
ARG BUILD_DATE
|
||||
ARG VERSION
|
||||
ARG REVISION
|
||||
|
||||
LABEL maintainer="stefanprodan"
|
||||
|
||||
RUN addgroup -S app \
|
||||
&& adduser -S -G app app \
|
||||
&& apk --no-cache add \
|
||||
ca-certificates curl netcat-openbsd
|
||||
|
||||
WORKDIR /home/app
|
||||
|
||||
COPY --from=builder /podinfo/bin/podinfo .
|
||||
COPY --from=builder /podinfo/bin/podcli /usr/local/bin/podcli
|
||||
COPY ./ui ./ui
|
||||
RUN chown -R app:app ./
|
||||
|
||||
USER app
|
||||
|
||||
CMD ["./podinfo"]
|
||||
@@ -1,10 +0,0 @@
|
||||
FROM golang:1.26
|
||||
|
||||
WORKDIR /workspace
|
||||
|
||||
# copy modules manifests
|
||||
COPY go.mod go.mod
|
||||
COPY go.sum go.sum
|
||||
|
||||
# cache modules
|
||||
RUN go mod download
|
||||
@@ -1,53 +0,0 @@
|
||||
ARG GO_VERSION=1.26
|
||||
ARG XX_VERSION=1.9.0
|
||||
|
||||
FROM --platform=$BUILDPLATFORM tonistiigi/xx:${XX_VERSION} AS xx
|
||||
|
||||
FROM --platform=$BUILDPLATFORM golang:${GO_VERSION}-alpine as builder
|
||||
|
||||
# Copy the build utilities.
|
||||
COPY --from=xx / /
|
||||
|
||||
ARG TARGETPLATFORM
|
||||
ARG REVISION
|
||||
|
||||
RUN mkdir -p /podinfo/
|
||||
|
||||
WORKDIR /podinfo
|
||||
|
||||
COPY . .
|
||||
|
||||
RUN go mod download
|
||||
|
||||
ENV CGO_ENABLED=0
|
||||
RUN xx-go build -ldflags "-s -w \
|
||||
-X github.com/stefanprodan/podinfo/pkg/version.REVISION=${REVISION}" \
|
||||
-a -o bin/podinfo cmd/podinfo/*
|
||||
|
||||
RUN xx-go build -ldflags "-s -w \
|
||||
-X github.com/stefanprodan/podinfo/pkg/version.REVISION=${REVISION}" \
|
||||
-a -o bin/podcli cmd/podcli/*
|
||||
|
||||
FROM alpine:3.23
|
||||
|
||||
ARG BUILD_DATE
|
||||
ARG VERSION
|
||||
ARG REVISION
|
||||
|
||||
LABEL maintainer="stefanprodan"
|
||||
|
||||
RUN addgroup -S app \
|
||||
&& adduser -S -G app app \
|
||||
&& apk --no-cache add \
|
||||
ca-certificates curl netcat-openbsd
|
||||
|
||||
WORKDIR /home/app
|
||||
|
||||
COPY --from=builder /podinfo/bin/podinfo .
|
||||
COPY --from=builder /podinfo/bin/podcli /usr/local/bin/podcli
|
||||
COPY ./ui ./ui
|
||||
RUN chown -R app:app ./
|
||||
|
||||
USER app
|
||||
|
||||
CMD ["./podinfo"]
|
||||
201
LICENSE
201
LICENSE
@@ -1,201 +0,0 @@
|
||||
Apache License
|
||||
Version 2.0, January 2004
|
||||
http://www.apache.org/licenses/
|
||||
|
||||
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
|
||||
|
||||
1. Definitions.
|
||||
|
||||
"License" shall mean the terms and conditions for use, reproduction,
|
||||
and distribution as defined by Sections 1 through 9 of this document.
|
||||
|
||||
"Licensor" shall mean the copyright owner or entity authorized by
|
||||
the copyright owner that is granting the License.
|
||||
|
||||
"Legal Entity" shall mean the union of the acting entity and all
|
||||
other entities that control, are controlled by, or are under common
|
||||
control with that entity. For the purposes of this definition,
|
||||
"control" means (i) the power, direct or indirect, to cause the
|
||||
direction or management of such entity, whether by contract or
|
||||
otherwise, or (ii) ownership of fifty percent (50%) or more of the
|
||||
outstanding shares, or (iii) beneficial ownership of such entity.
|
||||
|
||||
"You" (or "Your") shall mean an individual or Legal Entity
|
||||
exercising permissions granted by this License.
|
||||
|
||||
"Source" form shall mean the preferred form for making modifications,
|
||||
including but not limited to software source code, documentation
|
||||
source, and configuration files.
|
||||
|
||||
"Object" form shall mean any form resulting from mechanical
|
||||
transformation or translation of a Source form, including but
|
||||
not limited to compiled object code, generated documentation,
|
||||
and conversions to other media types.
|
||||
|
||||
"Work" shall mean the work of authorship, whether in Source or
|
||||
Object form, made available under the License, as indicated by a
|
||||
copyright notice that is included in or attached to the work
|
||||
(an example is provided in the Appendix below).
|
||||
|
||||
"Derivative Works" shall mean any work, whether in Source or Object
|
||||
form, that is based on (or derived from) the Work and for which the
|
||||
editorial revisions, annotations, elaborations, or other modifications
|
||||
represent, as a whole, an original work of authorship. For the purposes
|
||||
of this License, Derivative Works shall not include works that remain
|
||||
separable from, or merely link (or bind by name) to the interfaces of,
|
||||
the Work and Derivative Works thereof.
|
||||
|
||||
"Contribution" shall mean any work of authorship, including
|
||||
the original version of the Work and any modifications or additions
|
||||
to that Work or Derivative Works thereof, that is intentionally
|
||||
submitted to Licensor for inclusion in the Work by the copyright owner
|
||||
or by an individual or Legal Entity authorized to submit on behalf of
|
||||
the copyright owner. For the purposes of this definition, "submitted"
|
||||
means any form of electronic, verbal, or written communication sent
|
||||
to the Licensor or its representatives, including but not limited to
|
||||
communication on electronic mailing lists, source code control systems,
|
||||
and issue tracking systems that are managed by, or on behalf of, the
|
||||
Licensor for the purpose of discussing and improving the Work, but
|
||||
excluding communication that is conspicuously marked or otherwise
|
||||
designated in writing by the copyright owner as "Not a Contribution."
|
||||
|
||||
"Contributor" shall mean Licensor and any individual or Legal Entity
|
||||
on behalf of whom a Contribution has been received by Licensor and
|
||||
subsequently incorporated within the Work.
|
||||
|
||||
2. Grant of Copyright License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
copyright license to reproduce, prepare Derivative Works of,
|
||||
publicly display, publicly perform, sublicense, and distribute the
|
||||
Work and such Derivative Works in Source or Object form.
|
||||
|
||||
3. Grant of Patent License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
(except as stated in this section) patent license to make, have made,
|
||||
use, offer to sell, sell, import, and otherwise transfer the Work,
|
||||
where such license applies only to those patent claims licensable
|
||||
by such Contributor that are necessarily infringed by their
|
||||
Contribution(s) alone or by combination of their Contribution(s)
|
||||
with the Work to which such Contribution(s) was submitted. If You
|
||||
institute patent litigation against any entity (including a
|
||||
cross-claim or counterclaim in a lawsuit) alleging that the Work
|
||||
or a Contribution incorporated within the Work constitutes direct
|
||||
or contributory patent infringement, then any patent licenses
|
||||
granted to You under this License for that Work shall terminate
|
||||
as of the date such litigation is filed.
|
||||
|
||||
4. Redistribution. You may reproduce and distribute copies of the
|
||||
Work or Derivative Works thereof in any medium, with or without
|
||||
modifications, and in Source or Object form, provided that You
|
||||
meet the following conditions:
|
||||
|
||||
(a) You must give any other recipients of the Work or
|
||||
Derivative Works a copy of this License; and
|
||||
|
||||
(b) You must cause any modified files to carry prominent notices
|
||||
stating that You changed the files; and
|
||||
|
||||
(c) You must retain, in the Source form of any Derivative Works
|
||||
that You distribute, all copyright, patent, trademark, and
|
||||
attribution notices from the Source form of the Work,
|
||||
excluding those notices that do not pertain to any part of
|
||||
the Derivative Works; and
|
||||
|
||||
(d) If the Work includes a "NOTICE" text file as part of its
|
||||
distribution, then any Derivative Works that You distribute must
|
||||
include a readable copy of the attribution notices contained
|
||||
within such NOTICE file, excluding those notices that do not
|
||||
pertain to any part of the Derivative Works, in at least one
|
||||
of the following places: within a NOTICE text file distributed
|
||||
as part of the Derivative Works; within the Source form or
|
||||
documentation, if provided along with the Derivative Works; or,
|
||||
within a display generated by the Derivative Works, if and
|
||||
wherever such third-party notices normally appear. The contents
|
||||
of the NOTICE file are for informational purposes only and
|
||||
do not modify the License. You may add Your own attribution
|
||||
notices within Derivative Works that You distribute, alongside
|
||||
or as an addendum to the NOTICE text from the Work, provided
|
||||
that such additional attribution notices cannot be construed
|
||||
as modifying the License.
|
||||
|
||||
You may add Your own copyright statement to Your modifications and
|
||||
may provide additional or different license terms and conditions
|
||||
for use, reproduction, or distribution of Your modifications, or
|
||||
for any such Derivative Works as a whole, provided Your use,
|
||||
reproduction, and distribution of the Work otherwise complies with
|
||||
the conditions stated in this License.
|
||||
|
||||
5. Submission of Contributions. Unless You explicitly state otherwise,
|
||||
any Contribution intentionally submitted for inclusion in the Work
|
||||
by You to the Licensor shall be under the terms and conditions of
|
||||
this License, without any additional terms or conditions.
|
||||
Notwithstanding the above, nothing herein shall supersede or modify
|
||||
the terms of any separate license agreement you may have executed
|
||||
with Licensor regarding such Contributions.
|
||||
|
||||
6. Trademarks. This License does not grant permission to use the trade
|
||||
names, trademarks, service marks, or product names of the Licensor,
|
||||
except as required for reasonable and customary use in describing the
|
||||
origin of the Work and reproducing the content of the NOTICE file.
|
||||
|
||||
7. Disclaimer of Warranty. Unless required by applicable law or
|
||||
agreed to in writing, Licensor provides the Work (and each
|
||||
Contributor provides its Contributions) on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or
|
||||
implied, including, without limitation, any warranties or conditions
|
||||
of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A
|
||||
PARTICULAR PURPOSE. You are solely responsible for determining the
|
||||
appropriateness of using or redistributing the Work and assume any
|
||||
risks associated with Your exercise of permissions under this License.
|
||||
|
||||
8. Limitation of Liability. In no event and under no legal theory,
|
||||
whether in tort (including negligence), contract, or otherwise,
|
||||
unless required by applicable law (such as deliberate and grossly
|
||||
negligent acts) or agreed to in writing, shall any Contributor be
|
||||
liable to You for damages, including any direct, indirect, special,
|
||||
incidental, or consequential damages of any character arising as a
|
||||
result of this License or out of the use or inability to use the
|
||||
Work (including but not limited to damages for loss of goodwill,
|
||||
work stoppage, computer failure or malfunction, or any and all
|
||||
other commercial damages or losses), even if such Contributor
|
||||
has been advised of the possibility of such damages.
|
||||
|
||||
9. Accepting Warranty or Additional Liability. While redistributing
|
||||
the Work or Derivative Works thereof, You may choose to offer,
|
||||
and charge a fee for, acceptance of support, warranty, indemnity,
|
||||
or other liability obligations and/or rights consistent with this
|
||||
License. However, in accepting such obligations, You may act only
|
||||
on Your own behalf and on Your sole responsibility, not on behalf
|
||||
of any other Contributor, and only if You agree to indemnify,
|
||||
defend, and hold each Contributor harmless for any liability
|
||||
incurred by, or claims asserted against, such Contributor by reason
|
||||
of your accepting any such warranty or additional liability.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
|
||||
APPENDIX: How to apply the Apache License to your work.
|
||||
|
||||
To apply the Apache License to your work, attach the following
|
||||
boilerplate notice, with the fields enclosed by brackets "[]"
|
||||
replaced with your own identifying information. (Don't include
|
||||
the brackets!) The text should be enclosed in the appropriate
|
||||
comment syntax for the file format. We also recommend that a
|
||||
file or class name and description of purpose be included on the
|
||||
same "printed page" as the copyright notice for easier
|
||||
identification within third-party archives.
|
||||
|
||||
Copyright 2018 Stefan Prodan. All rights reserved.
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
104
Makefile
104
Makefile
@@ -1,104 +0,0 @@
|
||||
# Makefile for releasing podinfo
|
||||
#
|
||||
# The release version is controlled from pkg/version
|
||||
|
||||
TAG?=latest
|
||||
NAME:=podinfo
|
||||
DOCKER_REPOSITORY:=stefanprodan
|
||||
DOCKER_IMAGE_NAME:=$(DOCKER_REPOSITORY)/$(NAME)
|
||||
GIT_COMMIT:=$(shell git describe --dirty --always)
|
||||
VERSION:=$(shell grep 'VERSION' pkg/version/version.go | awk '{ print $$4 }' | tr -d '"')
|
||||
EXTRA_RUN_ARGS?=
|
||||
|
||||
run:
|
||||
go run -ldflags "-s -w -X github.com/stefanprodan/podinfo/pkg/version.REVISION=$(GIT_COMMIT)" cmd/podinfo/* \
|
||||
--level=debug --grpc-port=9999 --backend-url=https://httpbin.org/status/401 --backend-url=https://httpbin.org/status/500 \
|
||||
--ui-logo=https://raw.githubusercontent.com/stefanprodan/podinfo/gh-pages/cuddle_clap.gif $(EXTRA_RUN_ARGS)
|
||||
|
||||
.PHONY: test
|
||||
test: tidy fmt vet
|
||||
go test ./... -coverprofile cover.out
|
||||
|
||||
build:
|
||||
GIT_COMMIT=$$(git rev-list -1 HEAD) && CGO_ENABLED=0 go build -ldflags "-s -w -X github.com/stefanprodan/podinfo/pkg/version.REVISION=$(GIT_COMMIT)" -a -o ./bin/podinfo ./cmd/podinfo/*
|
||||
GIT_COMMIT=$$(git rev-list -1 HEAD) && CGO_ENABLED=0 go build -ldflags "-s -w -X github.com/stefanprodan/podinfo/pkg/version.REVISION=$(GIT_COMMIT)" -a -o ./bin/podcli ./cmd/podcli/*
|
||||
|
||||
tidy:
|
||||
rm -f go.sum; go mod tidy -compat=1.26
|
||||
|
||||
vet:
|
||||
go vet ./...
|
||||
|
||||
fmt:
|
||||
go fmt ./...
|
||||
|
||||
build-charts:
|
||||
helm lint charts/*
|
||||
helm package charts/*
|
||||
|
||||
build-container:
|
||||
docker build -t $(DOCKER_IMAGE_NAME):$(VERSION) .
|
||||
|
||||
build-xx:
|
||||
docker buildx build \
|
||||
--platform=linux/amd64 \
|
||||
-t $(DOCKER_IMAGE_NAME):$(VERSION) \
|
||||
--load \
|
||||
-f Dockerfile.xx .
|
||||
|
||||
build-base:
|
||||
docker build -f Dockerfile.base -t $(DOCKER_REPOSITORY)/podinfo-base:latest .
|
||||
|
||||
push-base: build-base
|
||||
docker push $(DOCKER_REPOSITORY)/podinfo-base:latest
|
||||
|
||||
test-container:
|
||||
@docker rm -f podinfo || true
|
||||
@docker run -dp 9898:9898 --name=podinfo $(DOCKER_IMAGE_NAME):$(VERSION)
|
||||
@docker ps
|
||||
@TOKEN=$$(curl -sd 'test' localhost:9898/token | jq -r .token) && \
|
||||
curl -sH "Authorization: Bearer $${TOKEN}" localhost:9898/token/validate | grep test
|
||||
|
||||
push-container:
|
||||
docker tag $(DOCKER_IMAGE_NAME):$(VERSION) $(DOCKER_IMAGE_NAME):latest
|
||||
docker push $(DOCKER_IMAGE_NAME):$(VERSION)
|
||||
docker push $(DOCKER_IMAGE_NAME):latest
|
||||
docker tag $(DOCKER_IMAGE_NAME):$(VERSION) quay.io/$(DOCKER_IMAGE_NAME):$(VERSION)
|
||||
docker tag $(DOCKER_IMAGE_NAME):$(VERSION) quay.io/$(DOCKER_IMAGE_NAME):latest
|
||||
docker push quay.io/$(DOCKER_IMAGE_NAME):$(VERSION)
|
||||
docker push quay.io/$(DOCKER_IMAGE_NAME):latest
|
||||
|
||||
version-set:
|
||||
@next="$(TAG)" && \
|
||||
current="$(VERSION)" && \
|
||||
/usr/bin/sed -i '' "s/$$current/$$next/g" pkg/version/version.go && \
|
||||
/usr/bin/sed -i '' "s/tag: $$current/tag: $$next/g" charts/podinfo/values.yaml && \
|
||||
/usr/bin/sed -i '' "s/tag: $$current/tag: $$next/g" charts/podinfo/values-prod.yaml && \
|
||||
/usr/bin/sed -i '' "s/appVersion: $$current/appVersion: $$next/g" charts/podinfo/Chart.yaml && \
|
||||
/usr/bin/sed -i '' "s/version: $$current/version: $$next/g" charts/podinfo/Chart.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" kustomize/deployment.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/webapp/frontend/deployment.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/webapp/backend/deployment.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/frontend/deployment.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/backend/deployment.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/database/statefulset-primary.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/database/deployment-replica.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/database/cronjob-rollup-daily.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/database/cronjob-rollup-weekly.yaml && \
|
||||
/usr/bin/sed -i '' "s/podinfo:$$current/podinfo:$$next/g" deploy/bases/database/cronjob-backup-daily.yaml && \
|
||||
/usr/bin/sed -i '' "s/$$current/$$next/g" timoni/podinfo/values.cue && \
|
||||
echo "Version $$next set in code, deployment, module, chart and kustomize"
|
||||
|
||||
release:
|
||||
git tag -s -m $(VERSION) $(VERSION)
|
||||
git push origin $(VERSION)
|
||||
|
||||
swagger:
|
||||
go install github.com/swaggo/swag/cmd/swag@latest
|
||||
go get github.com/swaggo/swag/gen@latest
|
||||
go get github.com/swaggo/swag/cmd/swag@latest
|
||||
cd pkg/api/http && $$(go env GOPATH)/bin/swag init -g server.go
|
||||
|
||||
.PHONY: timoni-build
|
||||
timoni-build:
|
||||
@timoni build podinfo ./timoni/podinfo -f ./timoni/podinfo/debug_values.cue
|
||||
212
README.md
212
README.md
@@ -1,212 +0,0 @@
|
||||
# podinfo
|
||||
|
||||
[](https://github.com/stefanprodan/podinfo/blob/master/.github/workflows/e2e.yml)
|
||||
[](https://github.com/stefanprodan/podinfo/blob/master/.github/workflows/test.yml)
|
||||
[](https://github.com/stefanprodan/podinfo/blob/master/.github/workflows/cve-scan.yml)
|
||||
[](https://goreportcard.com/report/github.com/stefanprodan/podinfo)
|
||||
[](https://hub.docker.com/r/stefanprodan/podinfo)
|
||||
|
||||
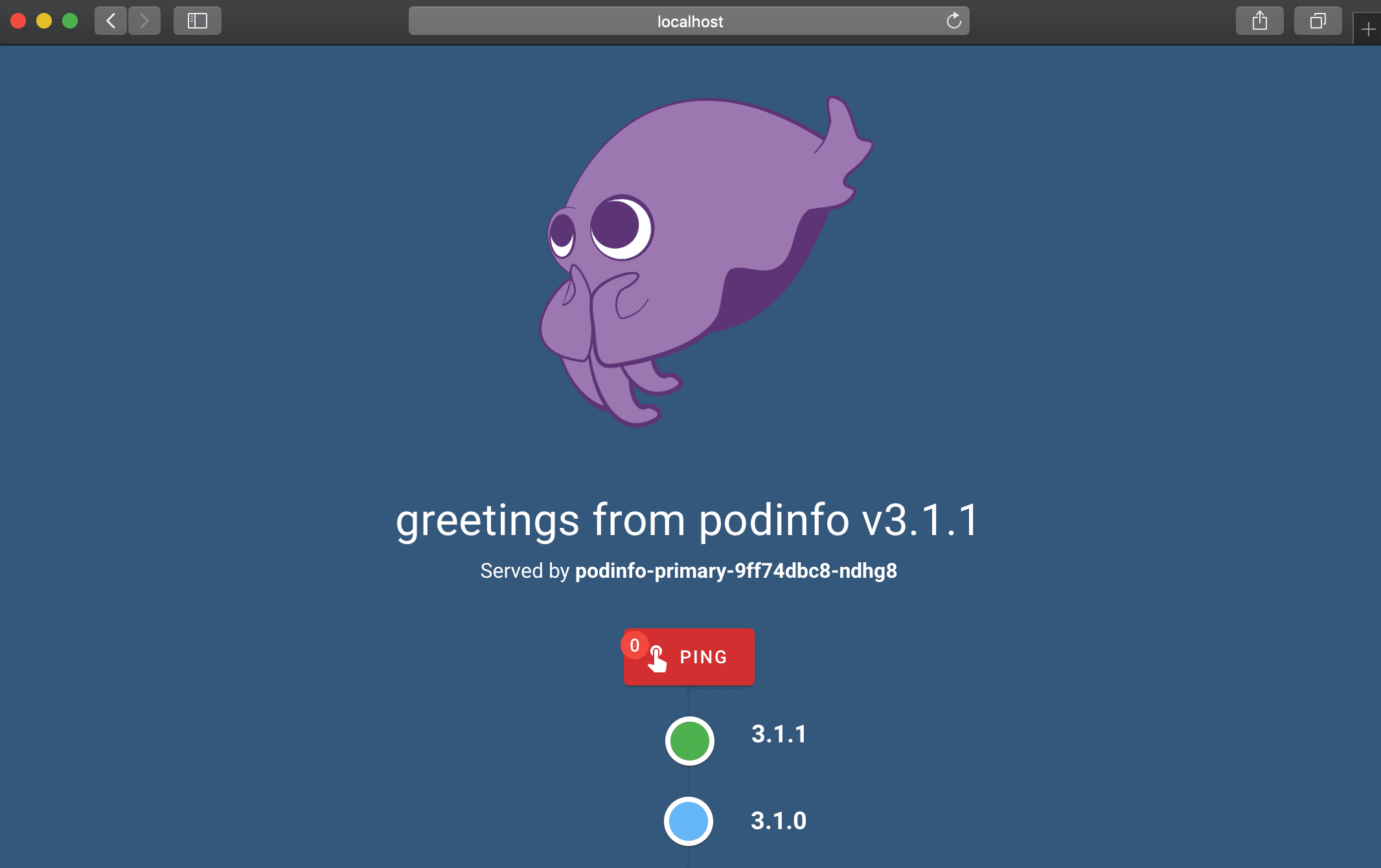
Podinfo is a tiny web application made with Go that showcases best practices of running microservices in Kubernetes.
|
||||
Podinfo is used by CNCF projects like [Flux](https://github.com/fluxcd/flux2) and [Flagger](https://github.com/fluxcd/flagger)
|
||||
for end-to-end testing and workshops.
|
||||
|
||||
Specifications:
|
||||
|
||||
* Health checks (readiness and liveness)
|
||||
* Graceful shutdown on interrupt signals
|
||||
* File watcher for secrets and configmaps
|
||||
* Instrumented with Prometheus and Open Telemetry
|
||||
* Structured logging with zap
|
||||
* 12-factor app with viper
|
||||
* Fault injection (random errors and latency)
|
||||
* Swagger docs
|
||||
* Timoni, Helm and Kustomize installers
|
||||
* End-to-End testing with Kubernetes Kind and Helm
|
||||
* Multi-arch container image with Docker buildx and GitHub Actions
|
||||
* Container image signing with Sigstore cosign
|
||||
* SBOMs and SLSA Provenance embedded in the container image
|
||||
* CVE scanning with govulncheck
|
||||
|
||||
Web API:
|
||||
|
||||
* `GET /` prints runtime information
|
||||
* `GET /version` prints podinfo version and git commit hash
|
||||
* `GET /metrics` return HTTP requests duration and Go runtime metrics
|
||||
* `GET /healthz` used by Kubernetes liveness probe
|
||||
* `GET /readyz` used by Kubernetes readiness probe
|
||||
* `POST /readyz/enable` signals the Kubernetes LB that this instance is ready to receive traffic
|
||||
* `POST /readyz/disable` signals the Kubernetes LB to stop sending requests to this instance
|
||||
* `GET /status/{code}` returns the status code
|
||||
* `GET /panic` crashes the process with exit code 255
|
||||
* `POST /echo` forwards the call to the backend service and echos the posted content
|
||||
* `GET /env` returns the environment variables as a JSON array
|
||||
* `GET /headers` returns a JSON with the request HTTP headers
|
||||
* `GET /delay/{seconds}` waits for the specified period
|
||||
* `POST /token` issues a JWT token valid for one minute `JWT=$(curl -sd 'anon' podinfo:9898/token | jq -r .token)`
|
||||
* `GET /token/validate` validates the JWT token `curl -H "Authorization: Bearer $JWT" podinfo:9898/token/validate`
|
||||
* `GET /configs` returns a JSON with configmaps and/or secrets mounted in the `config` volume
|
||||
* `POST/PUT /cache/{key}` saves the posted content to Redis
|
||||
* `GET /cache/{key}` returns the content from Redis if the key exists
|
||||
* `DELETE /cache/{key}` deletes the key from Redis if exists
|
||||
* `POST /store` writes the posted content to disk at /data/hash and returns the SHA1 hash of the content
|
||||
* `GET /store/{hash}` returns the content of the file /data/hash if exists
|
||||
* `GET /ws/echo` echos content via websockets `podcli ws ws://localhost:9898/ws/echo`
|
||||
* `GET /chunked/{seconds}` uses `transfer-encoding` type `chunked` to give a partial response and then waits for the specified period
|
||||
* `GET /swagger.json` returns the API Swagger docs, used for Linkerd service profiling and Gloo routes discovery
|
||||
|
||||
gRPC API:
|
||||
|
||||
* `/grpc.health.v1.Health/Check` health checking
|
||||
* `/grpc.EchoService/Echo` echos the received content
|
||||
* `/grpc.VersionService/Version` returns podinfo version and Git commit hash
|
||||
* `/grpc.DelayService/Delay` returns a successful response after the given seconds in the body of gRPC request
|
||||
* `/grpc.EnvService/Env` returns environment variables as a JSON array
|
||||
* `/grpc.HeaderService/Header` returns the headers present in the gRPC request. Any custom header can also be given as a part of request and that can be returned using this API
|
||||
* `/grpc.InfoService/Info` returns the runtime information
|
||||
* `/grpc.PanicService/Panic` crashes the process with gRPC status code as '1 CANCELLED'
|
||||
* `/grpc.StatusService/Status` returns the gRPC Status code given in the request body
|
||||
* `/grpc.TokenService/TokenGenerate` issues a JWT token valid for one minute
|
||||
* `/grpc.TokenService/TokenValidate` validates the JWT token
|
||||
|
||||
Web UI:
|
||||
|
||||
|
||||
|
||||
To access the Swagger UI open `<podinfo-host>/swagger/index.html` in a browser.
|
||||
|
||||
### Guides
|
||||
|
||||
* [Getting started with Timoni](https://timoni.sh/quickstart/)
|
||||
* [Getting started with Flux](https://fluxcd.io/flux/get-started/)
|
||||
* [Progressive Deliver with Flagger and Linkerd](https://docs.flagger.app/tutorials/linkerd-progressive-delivery)
|
||||
* [Automated canary deployments with Kubernetes Gateway API](https://docs.flagger.app/tutorials/gatewayapi-progressive-delivery)
|
||||
|
||||
### Install
|
||||
|
||||
To install Podinfo on Kubernetes the minimum required version is **Kubernetes v1.23**.
|
||||
|
||||
#### Timoni
|
||||
|
||||
Install with [Timoni](https://timoni.sh):
|
||||
|
||||
```bash
|
||||
timoni -n default apply podinfo oci://ghcr.io/stefanprodan/modules/podinfo
|
||||
```
|
||||
|
||||
#### Helm
|
||||
|
||||
Install from github.io:
|
||||
|
||||
```bash
|
||||
helm repo add podinfo https://stefanprodan.github.io/podinfo
|
||||
|
||||
helm upgrade --install --wait frontend \
|
||||
--namespace test \
|
||||
--set replicaCount=2 \
|
||||
--set backend=http://backend-podinfo:9898/echo \
|
||||
podinfo/podinfo
|
||||
|
||||
helm test frontend --namespace test
|
||||
|
||||
helm upgrade --install --wait backend \
|
||||
--namespace test \
|
||||
--set redis.enabled=true \
|
||||
podinfo/podinfo
|
||||
```
|
||||
|
||||
Install from ghcr.io:
|
||||
|
||||
```bash
|
||||
helm upgrade --install --wait podinfo --namespace default \
|
||||
oci://ghcr.io/stefanprodan/charts/podinfo
|
||||
```
|
||||
|
||||
#### Kustomize
|
||||
|
||||
```bash
|
||||
kubectl apply -k github.com/stefanprodan/podinfo//kustomize
|
||||
```
|
||||
|
||||
#### Docker
|
||||
|
||||
```bash
|
||||
docker run -dp 9898:9898 stefanprodan/podinfo
|
||||
```
|
||||
|
||||
### Continuous Delivery
|
||||
|
||||
In order to install podinfo on a Kubernetes cluster and keep it up to date with the latest
|
||||
release in an automated manner, you can use [Flux](https://fluxcd.io).
|
||||
|
||||
Install the Flux CLI on MacOS and Linux using Homebrew:
|
||||
|
||||
```sh
|
||||
brew install fluxcd/tap/flux
|
||||
```
|
||||
|
||||
Install the Flux controllers needed for Helm operations:
|
||||
|
||||
```sh
|
||||
flux install \
|
||||
--namespace=flux-system \
|
||||
--network-policy=false \
|
||||
--components=source-controller,helm-controller
|
||||
```
|
||||
|
||||
Add podinfo's Helm repository to your cluster and
|
||||
configure Flux to check for new chart releases every ten minutes:
|
||||
|
||||
```sh
|
||||
flux create source helm podinfo \
|
||||
--namespace=default \
|
||||
--url=https://stefanprodan.github.io/podinfo \
|
||||
--interval=10m
|
||||
```
|
||||
|
||||
Create a `podinfo-values.yaml` file locally:
|
||||
|
||||
```sh
|
||||
cat > podinfo-values.yaml <<EOL
|
||||
replicaCount: 2
|
||||
resources:
|
||||
limits:
|
||||
memory: 256Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 64Mi
|
||||
EOL
|
||||
```
|
||||
|
||||
Create a Helm release for deploying podinfo in the default namespace:
|
||||
|
||||
```sh
|
||||
flux create helmrelease podinfo \
|
||||
--namespace=default \
|
||||
--source=HelmRepository/podinfo \
|
||||
--release-name=podinfo \
|
||||
--chart=podinfo \
|
||||
--chart-version=">5.0.0" \
|
||||
--values=podinfo-values.yaml
|
||||
```
|
||||
|
||||
Based on the above definition, Flux will upgrade the release automatically
|
||||
when a new version of podinfo is released. If the upgrade fails, Flux
|
||||
can [rollback](https://toolkit.fluxcd.io/components/helm/helmreleases/#configuring-failure-remediation)
|
||||
to the previous working version.
|
||||
|
||||
You can check what version is currently deployed with:
|
||||
|
||||
```sh
|
||||
flux get helmreleases -n default
|
||||
```
|
||||
|
||||
To delete podinfo's Helm repository and release from your cluster run:
|
||||
|
||||
```sh
|
||||
flux -n default delete source helm podinfo
|
||||
flux -n default delete helmrelease podinfo
|
||||
```
|
||||
|
||||
If you wish to manage the lifecycle of your applications in a **GitOps** manner, check out
|
||||
this [workflow example](https://github.com/fluxcd/flux2-kustomize-helm-example)
|
||||
for multi-env deployments with Flux, Kustomize and Helm.
|
||||
@@ -1,21 +0,0 @@
|
||||
# Patterns to ignore when building packages.
|
||||
# This supports shell glob matching, relative path matching, and
|
||||
# negation (prefixed with !). Only one pattern per line.
|
||||
.DS_Store
|
||||
# Common VCS dirs
|
||||
.git/
|
||||
.gitignore
|
||||
.bzr/
|
||||
.bzrignore
|
||||
.hg/
|
||||
.hgignore
|
||||
.svn/
|
||||
# Common backup files
|
||||
*.swp
|
||||
*.bak
|
||||
*.tmp
|
||||
*~
|
||||
# Various IDEs
|
||||
.project
|
||||
.idea/
|
||||
*.tmproj
|
||||
@@ -1,13 +0,0 @@
|
||||
apiVersion: v1
|
||||
version: 6.11.0
|
||||
appVersion: 6.11.0
|
||||
name: podinfo
|
||||
engine: gotpl
|
||||
description: Podinfo Helm chart for Kubernetes
|
||||
home: https://github.com/stefanprodan/podinfo
|
||||
maintainers:
|
||||
- email: stefanprodan@users.noreply.github.com
|
||||
name: stefanprodan
|
||||
sources:
|
||||
- https://github.com/stefanprodan/podinfo
|
||||
kubeVersion: ">=1.23.0-0"
|
||||
@@ -1,201 +0,0 @@
|
||||
Apache License
|
||||
Version 2.0, January 2004
|
||||
http://www.apache.org/licenses/
|
||||
|
||||
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
|
||||
|
||||
1. Definitions.
|
||||
|
||||
"License" shall mean the terms and conditions for use, reproduction,
|
||||
and distribution as defined by Sections 1 through 9 of this document.
|
||||
|
||||
"Licensor" shall mean the copyright owner or entity authorized by
|
||||
the copyright owner that is granting the License.
|
||||
|
||||
"Legal Entity" shall mean the union of the acting entity and all
|
||||
other entities that control, are controlled by, or are under common
|
||||
control with that entity. For the purposes of this definition,
|
||||
"control" means (i) the power, direct or indirect, to cause the
|
||||
direction or management of such entity, whether by contract or
|
||||
otherwise, or (ii) ownership of fifty percent (50%) or more of the
|
||||
outstanding shares, or (iii) beneficial ownership of such entity.
|
||||
|
||||
"You" (or "Your") shall mean an individual or Legal Entity
|
||||
exercising permissions granted by this License.
|
||||
|
||||
"Source" form shall mean the preferred form for making modifications,
|
||||
including but not limited to software source code, documentation
|
||||
source, and configuration files.
|
||||
|
||||
"Object" form shall mean any form resulting from mechanical
|
||||
transformation or translation of a Source form, including but
|
||||
not limited to compiled object code, generated documentation,
|
||||
and conversions to other media types.
|
||||
|
||||
"Work" shall mean the work of authorship, whether in Source or
|
||||
Object form, made available under the License, as indicated by a
|
||||
copyright notice that is included in or attached to the work
|
||||
(an example is provided in the Appendix below).
|
||||
|
||||
"Derivative Works" shall mean any work, whether in Source or Object
|
||||
form, that is based on (or derived from) the Work and for which the
|
||||
editorial revisions, annotations, elaborations, or other modifications
|
||||
represent, as a whole, an original work of authorship. For the purposes
|
||||
of this License, Derivative Works shall not include works that remain
|
||||
separable from, or merely link (or bind by name) to the interfaces of,
|
||||
the Work and Derivative Works thereof.
|
||||
|
||||
"Contribution" shall mean any work of authorship, including
|
||||
the original version of the Work and any modifications or additions
|
||||
to that Work or Derivative Works thereof, that is intentionally
|
||||
submitted to Licensor for inclusion in the Work by the copyright owner
|
||||
or by an individual or Legal Entity authorized to submit on behalf of
|
||||
the copyright owner. For the purposes of this definition, "submitted"
|
||||
means any form of electronic, verbal, or written communication sent
|
||||
to the Licensor or its representatives, including but not limited to
|
||||
communication on electronic mailing lists, source code control systems,
|
||||
and issue tracking systems that are managed by, or on behalf of, the
|
||||
Licensor for the purpose of discussing and improving the Work, but
|
||||
excluding communication that is conspicuously marked or otherwise
|
||||
designated in writing by the copyright owner as "Not a Contribution."
|
||||
|
||||
"Contributor" shall mean Licensor and any individual or Legal Entity
|
||||
on behalf of whom a Contribution has been received by Licensor and
|
||||
subsequently incorporated within the Work.
|
||||
|
||||
2. Grant of Copyright License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
copyright license to reproduce, prepare Derivative Works of,
|
||||
publicly display, publicly perform, sublicense, and distribute the
|
||||
Work and such Derivative Works in Source or Object form.
|
||||
|
||||
3. Grant of Patent License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
(except as stated in this section) patent license to make, have made,
|
||||
use, offer to sell, sell, import, and otherwise transfer the Work,
|
||||
where such license applies only to those patent claims licensable
|
||||
by such Contributor that are necessarily infringed by their
|
||||
Contribution(s) alone or by combination of their Contribution(s)
|
||||
with the Work to which such Contribution(s) was submitted. If You
|
||||
institute patent litigation against any entity (including a
|
||||
cross-claim or counterclaim in a lawsuit) alleging that the Work
|
||||
or a Contribution incorporated within the Work constitutes direct
|
||||
or contributory patent infringement, then any patent licenses
|
||||
granted to You under this License for that Work shall terminate
|
||||
as of the date such litigation is filed.
|
||||
|
||||
4. Redistribution. You may reproduce and distribute copies of the
|
||||
Work or Derivative Works thereof in any medium, with or without
|
||||
modifications, and in Source or Object form, provided that You
|
||||
meet the following conditions:
|
||||
|
||||
(a) You must give any other recipients of the Work or
|
||||
Derivative Works a copy of this License; and
|
||||
|
||||
(b) You must cause any modified files to carry prominent notices
|
||||
stating that You changed the files; and
|
||||
|
||||
(c) You must retain, in the Source form of any Derivative Works
|
||||
that You distribute, all copyright, patent, trademark, and
|
||||
attribution notices from the Source form of the Work,
|
||||
excluding those notices that do not pertain to any part of
|
||||
the Derivative Works; and
|
||||
|
||||
(d) If the Work includes a "NOTICE" text file as part of its
|
||||
distribution, then any Derivative Works that You distribute must
|
||||
include a readable copy of the attribution notices contained
|
||||
within such NOTICE file, excluding those notices that do not
|
||||
pertain to any part of the Derivative Works, in at least one
|
||||
of the following places: within a NOTICE text file distributed
|
||||
as part of the Derivative Works; within the Source form or
|
||||
documentation, if provided along with the Derivative Works; or,
|
||||
within a display generated by the Derivative Works, if and
|
||||
wherever such third-party notices normally appear. The contents
|
||||
of the NOTICE file are for informational purposes only and
|
||||
do not modify the License. You may add Your own attribution
|
||||
notices within Derivative Works that You distribute, alongside
|
||||
or as an addendum to the NOTICE text from the Work, provided
|
||||
that such additional attribution notices cannot be construed
|
||||
as modifying the License.
|
||||
|
||||
You may add Your own copyright statement to Your modifications and
|
||||
may provide additional or different license terms and conditions
|
||||
for use, reproduction, or distribution of Your modifications, or
|
||||
for any such Derivative Works as a whole, provided Your use,
|
||||
reproduction, and distribution of the Work otherwise complies with
|
||||
the conditions stated in this License.
|
||||
|
||||
5. Submission of Contributions. Unless You explicitly state otherwise,
|
||||
any Contribution intentionally submitted for inclusion in the Work
|
||||
by You to the Licensor shall be under the terms and conditions of
|
||||
this License, without any additional terms or conditions.
|
||||
Notwithstanding the above, nothing herein shall supersede or modify
|
||||
the terms of any separate license agreement you may have executed
|
||||
with Licensor regarding such Contributions.
|
||||
|
||||
6. Trademarks. This License does not grant permission to use the trade
|
||||
names, trademarks, service marks, or product names of the Licensor,
|
||||
except as required for reasonable and customary use in describing the
|
||||
origin of the Work and reproducing the content of the NOTICE file.
|
||||
|
||||
7. Disclaimer of Warranty. Unless required by applicable law or
|
||||
agreed to in writing, Licensor provides the Work (and each
|
||||
Contributor provides its Contributions) on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or
|
||||
implied, including, without limitation, any warranties or conditions
|
||||
of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A
|
||||
PARTICULAR PURPOSE. You are solely responsible for determining the
|
||||
appropriateness of using or redistributing the Work and assume any
|
||||
risks associated with Your exercise of permissions under this License.
|
||||
|
||||
8. Limitation of Liability. In no event and under no legal theory,
|
||||
whether in tort (including negligence), contract, or otherwise,
|
||||
unless required by applicable law (such as deliberate and grossly
|
||||
negligent acts) or agreed to in writing, shall any Contributor be
|
||||
liable to You for damages, including any direct, indirect, special,
|
||||
incidental, or consequential damages of any character arising as a
|
||||
result of this License or out of the use or inability to use the
|
||||
Work (including but not limited to damages for loss of goodwill,
|
||||
work stoppage, computer failure or malfunction, or any and all
|
||||
other commercial damages or losses), even if such Contributor
|
||||
has been advised of the possibility of such damages.
|
||||
|
||||
9. Accepting Warranty or Additional Liability. While redistributing
|
||||
the Work or Derivative Works thereof, You may choose to offer,
|
||||
and charge a fee for, acceptance of support, warranty, indemnity,
|
||||
or other liability obligations and/or rights consistent with this
|
||||
License. However, in accepting such obligations, You may act only
|
||||
on Your own behalf and on Your sole responsibility, not on behalf
|
||||
of any other Contributor, and only if You agree to indemnify,
|
||||
defend, and hold each Contributor harmless for any liability
|
||||
incurred by, or claims asserted against, such Contributor by reason
|
||||
of your accepting any such warranty or additional liability.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
|
||||
APPENDIX: How to apply the Apache License to your work.
|
||||
|
||||
To apply the Apache License to your work, attach the following
|
||||
boilerplate notice, with the fields enclosed by brackets "[]"
|
||||
replaced with your own identifying information. (Don't include
|
||||
the brackets!) The text should be enclosed in the appropriate
|
||||
comment syntax for the file format. We also recommend that a
|
||||
file or class name and description of purpose be included on the
|
||||
same "printed page" as the copyright notice for easier
|
||||
identification within third-party archives.
|
||||
|
||||
Copyright 2018 Stefan Prodan. All rights reserved.
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
@@ -1,152 +0,0 @@
|
||||
# Podinfo
|
||||
|
||||
Podinfo is a tiny web application made with Go
|
||||
that showcases best practices of running microservices in Kubernetes.
|
||||
|
||||
Podinfo is used by CNCF projects like [Flux](https://github.com/fluxcd/flux2)
|
||||
and [Flagger](https://github.com/fluxcd/flagger)
|
||||
for end-to-end testing and workshops.
|
||||
|
||||
## Installing the Chart
|
||||
|
||||
The Podinfo charts are published to
|
||||
[GitHub Container Registry](https://github.com/stefanprodan/podinfo/pkgs/container/charts%2Fpodinfo)
|
||||
and signed with [Cosign](https://github.com/sigstore/cosign) & GitHub Actions OIDC.
|
||||
|
||||
To install the chart with the release name `podinfo` from GHCR:
|
||||
|
||||
```console
|
||||
$ helm upgrade -i podinfo oci://ghcr.io/stefanprodan/charts/podinfo
|
||||
```
|
||||
|
||||
To verify a chart version with Cosign:
|
||||
|
||||
```console
|
||||
$ cosign verify ghcr.io/stefanprodan/charts/podinfo:<VERSION> \
|
||||
--certificate-oidc-issuer=https://token.actions.githubusercontent.com \
|
||||
--certificate-identity-regexp=^https://github\\.com/stefanprodan/podinfo/.*$
|
||||
```
|
||||
|
||||
Alternatively, you can install the chart from GitHub pages:
|
||||
|
||||
```console
|
||||
$ helm repo add stefanprodan https://stefanprodan.github.io/podinfo
|
||||
|
||||
$ helm upgrade -i podinfo stefanprodan/podinfo
|
||||
```
|
||||
|
||||
The command deploys podinfo on the Kubernetes cluster in the default namespace.
|
||||
The [configuration](#configuration) section lists the parameters that can be configured during installation.
|
||||
|
||||
## Uninstalling the Chart
|
||||
|
||||
To uninstall the `podinfo` release:
|
||||
|
||||
```console
|
||||
$ helm uninstall podinfo
|
||||
```
|
||||
|
||||
The command removes all the Kubernetes components associated with the chart and deletes the release.
|
||||
|
||||
## Configuration
|
||||
|
||||
The following tables lists the configurable parameters of the podinfo chart and their default values.
|
||||
|
||||
| Parameter | Default | Description |
|
||||
|--------------------------------------------------|--------------------------------|---------------------------------------------------------------------------------------------------|
|
||||
| `replicaCount` | `1` | Desired number of pods |
|
||||
| `logLevel` | `info` | Log level: `debug`, `info`, `warn`, `error` |
|
||||
| `backend` | `None` | Echo backend URL |
|
||||
| `backends` | `[]` | Array of echo backend URLs |
|
||||
| `cache` | `None` | Redis address in the format `tcp://<host>:<port>` |
|
||||
| `redis.enabled` | `false` | Create Redis deployment for caching purposes |
|
||||
| `redis.repository` | `docker.io/redis` | Redis image repository |
|
||||
| `redis.tag` | `<VERSION>` | Redis image tag |
|
||||
| `redis.imagePullSecrets` | `[]` | Redis image pull secrets |
|
||||
| `ui.color` | `#34577c` | UI color |
|
||||
| `ui.message` | `None` | UI greetings message |
|
||||
| `ui.logo` | `None` | UI logo |
|
||||
| `faults.delay` | `false` | Random HTTP response delays between 0 and 5 seconds |
|
||||
| `faults.error` | `false` | 1/3 chances of a random HTTP response error |
|
||||
| `faults.unhealthy` | `false` | When set, the healthy state is never reached |
|
||||
| `faults.unready` | `false` | When set, the ready state is never reached |
|
||||
| `faults.testFail` | `false` | When set, a helm test is included which always fails |
|
||||
| `faults.testTimeout` | `false` | When set, a helm test is included which always times out |
|
||||
| `image.repository` | `ghcr.io/stefanprodan/podinfo` | Image repository |
|
||||
| `image.tag` | `<VERSION>` | Image tag |
|
||||
| `image.pullPolicy` | `IfNotPresent` | Image pull policy |
|
||||
| `image.pullSecrets` | `[]` | Image pull secrets |
|
||||
| `service.enabled` | `true` | Create a Kubernetes Service, should be disabled when using [Flagger](https://flagger.app) |
|
||||
| `service.type` | `ClusterIP` | Type of the Kubernetes Service |
|
||||
| `service.metricsPort` | `9797` | Prometheus metrics endpoint port |
|
||||
| `service.httpPort` | `9898` | Container HTTP port |
|
||||
| `service.externalPort` | `9898` | ClusterIP HTTP port |
|
||||
| `service.grpcPort` | `9999` | ClusterIP gPRC port |
|
||||
| `service.grpcService` | `podinfo` | gPRC service name |
|
||||
| `service.nodePort` | `31198` | NodePort for the HTTP endpoint |
|
||||
| `service.trafficDistribution` | `""` | Traffic distribution strategy |
|
||||
| `service.additionalLabels` | `{}` | Additional labels to add to the service |
|
||||
| `service.externalTrafficPolicy` | `None` | External traffic policy for LoadBalance service |
|
||||
| `h2c.enabled` | `false` | Allow upgrading to h2c (non-TLS version of HTTP/2) |
|
||||
| `extraArgs` | `[]` | Additional command line arguments to pass to podinfo container |
|
||||
| `extraEnvs` | `[]` | Extra environment variables for the podinfo container |
|
||||
| `config.path` | `""` | config file path |
|
||||
| `config.name` | `""` | config file name |
|
||||
| `hpa.enabled` | `false` | Enables the Kubernetes HPA |
|
||||
| `hpa.maxReplicas` | `10` | Maximum amount of pods |
|
||||
| `hpa.cpu` | `None` | Target CPU usage per pod |
|
||||
| `hpa.memory` | `None` | Target memory usage per pod |
|
||||
| `hpa.requests` | `None` | Target HTTP requests per second per pod |
|
||||
| `serviceAccount.enabled` | `false` | Whether a service account should be created |
|
||||
| `serviceAccount.name` | `None` | The name of the service account to use, if not set a name is generated using the fullname template|
|
||||
| `serviceAccount.imagePullSecrets` | `[]` | List of image pull secrets if pulling from private registries |
|
||||
| `securityContext` | `{}` | The security context to be set on the podinfo container |
|
||||
| `podSecurityContext` | `{}` | The security context to be set on the pod |
|
||||
| `podAnnotations` | `{}` | Pod annotations |
|
||||
| `serviceMonitor.enabled` | `false` | Whether a Prometheus Operator service monitor should be created |
|
||||
| `serviceMonitor.interval` | `15s` | Prometheus scraping interval |
|
||||
| `serviceMonitor.additionalLabels` | `{}` | Add additional labels to the service monitor |
|
||||
| `ingress.enabled` | `false` | Enables Ingress |
|
||||
| `ingress.className` | `""` | Use ingressClassName |
|
||||
| `ingress.additionalLabels` | `{}` | Add additional labels to the ingress |
|
||||
| `ingress.annotations` | `{}` | Ingress annotations |
|
||||
| `ingress.hosts` | `[]` | Ingress accepted hosts |
|
||||
| `ingress.tls` | `[]` | Ingress TLS configuration |
|
||||
| `httpRoute.enabled` | `false` | Enables Gateway API HTTPRoute |
|
||||
| `httpRoute.additionalLabels` | `{}` | Add additional labels to the HTTPRoute |
|
||||
| `httpRoute.annotations` | `{}` | HTTPRoute annotations |
|
||||
| `httpRoute.parentRefs` | `[]` | Gateways that this route is attached to |
|
||||
| `httpRoute.hostnames` | `["podinfo.local"]` | Hostnames matching HTTP header |
|
||||
| `httpRoute.rules` | `[]` | List of rules and filters applied |
|
||||
| `hooks.<hookType>.job.enabled` | `false` | Create a Helm hook job for testing (hookType: see values.yaml for available hooks) |
|
||||
| `hooks.<hookType>.job.hookDeletePolicy` | `hook-succeeded,hook-failed` | Helm hook delete policy |
|
||||
| `hooks.<hookType>.job.ttlSecondsAfterFinished` | `None` | Job TTL after finished |
|
||||
| `hooks.<hookType>.job.sleepSeconds` | `None` | Sleep duration before job exits |
|
||||
| `hooks.<hookType>.job.exitCode` | `0` | Job exit code |
|
||||
| `resources.requests.cpu` | `1m` | Pod CPU request |
|
||||
| `resources.requests.memory` | `16Mi` | Pod memory request |
|
||||
| `resources.limits.cpu` | `None` | Pod CPU limit |
|
||||
| `resources.limits.memory` | `None` | Pod memory limit |
|
||||
| `nodeSelector` | `{}` | Node labels for pod assignment |
|
||||
| `tolerations` | `[]` | List of node taints to tolerate |
|
||||
| `affinity` | `None` | Node/pod affinities |
|
||||
|
||||
Specify each parameter using the `--set key=value[,key=value]` argument:
|
||||
|
||||
```console
|
||||
$ helm upgrade -i podinfo oci://ghcr.io/stefanprodan/charts/podinfo \
|
||||
--set=serviceMonitor.enabled=true,serviceMonitor.interval=5s
|
||||
```
|
||||
|
||||
To add custom annotations you need to escape the annotation key string:
|
||||
|
||||
```console
|
||||
$ helm upgrade -i podinfo oci://ghcr.io/stefanprodan/charts/podinfo \
|
||||
--set podAnnotations."toolkit\.fluxcd\.io\/tenant"=dev-team
|
||||
```
|
||||
|
||||
Alternatively, a YAML file that specifies the values for the above parameters can be provided while installing the chart:
|
||||
|
||||
```console
|
||||
$ helm upgrade -i my-release oci://ghcr.io/stefanprodan/charts/podinfo -f values.yaml
|
||||
```
|
||||
@@ -1,20 +0,0 @@
|
||||
1. Get the application URL by running these commands:
|
||||
{{- if .Values.ingress.enabled }}
|
||||
{{- range $host := .Values.ingress.hosts }}
|
||||
{{- range .paths }}
|
||||
http{{ if $.Values.ingress.tls }}s{{ end }}://{{ $host.host }}{{ .path }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- else if contains "NodePort" .Values.service.type }}
|
||||
export NODE_PORT=$(kubectl get --namespace {{ include "podinfo.namespace" . }} -o jsonpath="{.spec.ports[0].nodePort}" services {{ template "podinfo.fullname" . }})
|
||||
export NODE_IP=$(kubectl get nodes --namespace {{ include "podinfo.namespace" . }} -o jsonpath="{.items[0].status.addresses[0].address}")
|
||||
echo http://$NODE_IP:$NODE_PORT
|
||||
{{- else if contains "LoadBalancer" .Values.service.type }}
|
||||
NOTE: It may take a few minutes for the LoadBalancer IP to be available.
|
||||
You can watch the status of by running 'kubectl get svc -w {{ template "podinfo.fullname" . }}'
|
||||
export SERVICE_IP=$(kubectl get svc --namespace {{ include "podinfo.namespace" . }} {{ template "podinfo.fullname" . }} -o jsonpath='{.status.loadBalancer.ingress[0].ip}')
|
||||
echo http://$SERVICE_IP:{{ .Values.service.externalPort }}
|
||||
{{- else if contains "ClusterIP" .Values.service.type }}
|
||||
echo "Visit http://127.0.0.1:8080 to use your application"
|
||||
kubectl -n {{ include "podinfo.namespace" . }} port-forward deploy/{{ template "podinfo.fullname" . }} 8080:{{ .Values.service.externalPort }}
|
||||
{{- end }}
|
||||
@@ -1,76 +0,0 @@
|
||||
{{/*
|
||||
Expand the name of the chart.
|
||||
*/}}
|
||||
{{- define "podinfo.name" -}}
|
||||
{{- default .Chart.Name .Values.nameOverride | trunc 63 | trimSuffix "-" }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Create a default fully qualified app name.
|
||||
We truncate at 63 chars because some Kubernetes name fields are limited to this (by the DNS naming spec).
|
||||
If release name contains chart name it will be used as a full name.
|
||||
*/}}
|
||||
{{- define "podinfo.fullname" -}}
|
||||
{{- if .Values.fullnameOverride }}
|
||||
{{- .Values.fullnameOverride | trunc 63 | trimSuffix "-" }}
|
||||
{{- else }}
|
||||
{{- $name := default .Chart.Name .Values.nameOverride }}
|
||||
{{- if contains $name .Release.Name }}
|
||||
{{- .Release.Name | trunc 63 | trimSuffix "-" }}
|
||||
{{- else }}
|
||||
{{- printf "%s-%s" .Release.Name $name | trunc 63 | trimSuffix "-" }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Allow the release namespace to be overridden for multi-namespace deployments in combined charts.
|
||||
*/}}
|
||||
{{- define "podinfo.namespace" -}}
|
||||
{{- default .Release.Namespace .Values.namespaceOverride | trunc 63 | trimSuffix "-" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Create chart name and version as used by the chart label.
|
||||
*/}}
|
||||
{{- define "podinfo.chart" -}}
|
||||
{{- printf "%s-%s" .Chart.Name .Chart.Version | replace "+" "_" | trunc 63 | trimSuffix "-" }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Common labels
|
||||
*/}}
|
||||
{{- define "podinfo.labels" -}}
|
||||
helm.sh/chart: {{ include "podinfo.chart" . }}
|
||||
{{ include "podinfo.selectorLabels" . }}
|
||||
{{- if .Chart.AppVersion }}
|
||||
app.kubernetes.io/version: {{ .Chart.AppVersion | quote }}
|
||||
{{- end }}
|
||||
app.kubernetes.io/managed-by: {{ .Release.Service }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Selector labels
|
||||
*/}}
|
||||
{{- define "podinfo.selectorLabels" -}}
|
||||
app.kubernetes.io/name: {{ include "podinfo.fullname" . }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Create the name of the service account to use
|
||||
*/}}
|
||||
{{- define "podinfo.serviceAccountName" -}}
|
||||
{{- if .Values.serviceAccount.enabled }}
|
||||
{{- default (include "podinfo.fullname" .) .Values.serviceAccount.name }}
|
||||
{{- else }}
|
||||
{{- default "default" .Values.serviceAccount.name }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Create the name of the tls secret for secure port
|
||||
*/}}
|
||||
{{- define "podinfo.tlsSecretName" -}}
|
||||
{{- $fullname := include "podinfo.fullname" . -}}
|
||||
{{- default (printf "%s-tls" $fullname) .Values.tls.secretName }}
|
||||
{{- end }}
|
||||
@@ -1,17 +0,0 @@
|
||||
{{- if .Values.certificate.create -}}
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
spec:
|
||||
dnsNames:
|
||||
{{- range .Values.certificate.dnsNames }}
|
||||
- {{ . | quote }}
|
||||
{{- end }}
|
||||
secretName: {{ template "podinfo.tlsSecretName" . }}
|
||||
issuerRef:
|
||||
{{- .Values.certificate.issuerRef | toYaml | trimSuffix "\n" | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -1,229 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
spec:
|
||||
{{- if not .Values.hpa.enabled }}
|
||||
replicas: {{ .Values.replicaCount }}
|
||||
{{- end }}
|
||||
strategy:
|
||||
type: RollingUpdate
|
||||
rollingUpdate:
|
||||
maxUnavailable: 1
|
||||
selector:
|
||||
matchLabels:
|
||||
{{- include "podinfo.selectorLabels" . | nindent 6 }}
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
{{- include "podinfo.selectorLabels" . | nindent 8 }}
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "{{ .Values.service.httpPort }}"
|
||||
{{- range $key, $value := .Values.podAnnotations }}
|
||||
{{ $key }}: {{ $value | quote }}
|
||||
{{- end }}
|
||||
spec:
|
||||
terminationGracePeriodSeconds: 30
|
||||
{{- if .Values.serviceAccount.enabled }}
|
||||
serviceAccountName: {{ template "podinfo.serviceAccountName" . }}
|
||||
{{- end }}
|
||||
{{- if .Values.image.pullSecrets }}
|
||||
imagePullSecrets: {{ toYaml .Values.image.pullSecrets | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: {{ .Chart.Name }}
|
||||
image: "{{ .Values.image.repository }}:{{ .Values.image.tag }}"
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
{{- if .Values.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml .Values.securityContext | nindent 12 }}
|
||||
{{- else if (or .Values.service.hostPort .Values.tls.hostPort) }}
|
||||
securityContext:
|
||||
allowPrivilegeEscalation: true
|
||||
capabilities:
|
||||
drop:
|
||||
- ALL
|
||||
add:
|
||||
- NET_BIND_SERVICE
|
||||
{{- end }}
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port={{ .Values.service.httpPort | default 9898 }}
|
||||
{{- if .Values.host }}
|
||||
- --host={{ .Values.host }}
|
||||
{{- end }}
|
||||
{{- if .Values.tls.enabled }}
|
||||
- --secure-port={{ .Values.tls.port }}
|
||||
{{- end }}
|
||||
{{- if .Values.tls.certPath }}
|
||||
- --cert-path={{ .Values.tls.certPath }}
|
||||
{{- end }}
|
||||
{{- if .Values.service.metricsPort }}
|
||||
- --port-metrics={{ .Values.service.metricsPort }}
|
||||
{{- end }}
|
||||
{{- if .Values.service.grpcPort }}
|
||||
- --grpc-port={{ .Values.service.grpcPort }}
|
||||
{{- end }}
|
||||
{{- if .Values.service.grpcService }}
|
||||
- --grpc-service-name={{ .Values.service.grpcService }}
|
||||
{{- end }}
|
||||
{{- range .Values.backends }}
|
||||
- --backend-url={{ . }}
|
||||
{{- end }}
|
||||
{{- if .Values.cache }}
|
||||
- --cache-server={{ .Values.cache }}
|
||||
{{- else if .Values.redis.enabled }}
|
||||
- --cache-server=tcp://{{ template "podinfo.fullname" . }}-redis:6379
|
||||
{{- end }}
|
||||
- --level={{ .Values.logLevel }}
|
||||
- --random-delay={{ .Values.faults.delay }}
|
||||
- --random-error={{ .Values.faults.error }}
|
||||
{{- if .Values.faults.unhealthy }}
|
||||
- --unhealthy
|
||||
{{- end }}
|
||||
{{- if .Values.faults.unready }}
|
||||
- --unready
|
||||
{{- end }}
|
||||
{{- if .Values.h2c.enabled }}
|
||||
- --h2c
|
||||
{{- end }}
|
||||
{{- with .Values.config.path }}
|
||||
- --config-path={{ . }}
|
||||
{{- end }}
|
||||
{{- with .Values.config.name }}
|
||||
- --config={{ . }}
|
||||
{{- end }}
|
||||
{{- with .Values.extraArgs }}
|
||||
{{- toYaml . | nindent 12 }}
|
||||
{{- end }}
|
||||
env:
|
||||
{{- if .Values.ui.message }}
|
||||
- name: PODINFO_UI_MESSAGE
|
||||
value: {{ quote .Values.ui.message }}
|
||||
{{- end }}
|
||||
{{- if .Values.ui.logo }}
|
||||
- name: PODINFO_UI_LOGO
|
||||
value: {{ .Values.ui.logo }}
|
||||
{{- end }}
|
||||
{{- if .Values.ui.color }}
|
||||
- name: PODINFO_UI_COLOR
|
||||
value: {{ quote .Values.ui.color }}
|
||||
{{- end }}
|
||||
{{- if .Values.backend }}
|
||||
- name: PODINFO_BACKEND_URL
|
||||
value: {{ .Values.backend }}
|
||||
{{- end }}
|
||||
{{- if .Values.extraEnvs }}
|
||||
{{ toYaml .Values.extraEnvs | indent 10 }}
|
||||
{{- end }}
|
||||
ports:
|
||||
- name: http
|
||||
containerPort: {{ .Values.service.httpPort | default 9898 }}
|
||||
protocol: TCP
|
||||
{{- if .Values.service.hostPort }}
|
||||
hostPort: {{ .Values.service.hostPort }}
|
||||
{{- end }}
|
||||
{{- if .Values.tls.enabled }}
|
||||
- name: https
|
||||
containerPort: {{ .Values.tls.port | default 9899 }}
|
||||
protocol: TCP
|
||||
{{- if .Values.tls.hostPort }}
|
||||
hostPort: {{ .Values.tls.hostPort }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.service.metricsPort }}
|
||||
- name: http-metrics
|
||||
containerPort: {{ .Values.service.metricsPort }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
{{- if .Values.service.grpcPort }}
|
||||
- name: grpc
|
||||
containerPort: {{ .Values.service.grpcPort }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
{{- if .Values.probes.startup.enable }}
|
||||
startupProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:{{ .Values.service.httpPort | default 9898 }}/healthz
|
||||
{{- with .Values.probes.startup }}
|
||||
initialDelaySeconds: {{ .initialDelaySeconds | default 1 }}
|
||||
timeoutSeconds: {{ .timeoutSeconds | default 5 }}
|
||||
failureThreshold: {{ .failureThreshold | default 3 }}
|
||||
successThreshold: {{ .successThreshold | default 1 }}
|
||||
periodSeconds: {{ .periodSeconds | default 10 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:{{ .Values.service.httpPort | default 9898 }}/healthz
|
||||
{{- with .Values.probes.liveness }}
|
||||
initialDelaySeconds: {{ .initialDelaySeconds | default 1 }}
|
||||
timeoutSeconds: {{ .timeoutSeconds | default 5 }}
|
||||
failureThreshold: {{ .failureThreshold | default 3 }}
|
||||
successThreshold: {{ .successThreshold | default 1 }}
|
||||
periodSeconds: {{ .periodSeconds | default 10 }}
|
||||
{{- end }}
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:{{ .Values.service.httpPort | default 9898 }}/readyz
|
||||
{{- with .Values.probes.readiness }}
|
||||
initialDelaySeconds: {{ .initialDelaySeconds | default 1 }}
|
||||
timeoutSeconds: {{ .timeoutSeconds | default 5 }}
|
||||
failureThreshold: {{ .failureThreshold | default 3 }}
|
||||
successThreshold: {{ .successThreshold | default 1 }}
|
||||
periodSeconds: {{ .periodSeconds | default 10 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: data
|
||||
mountPath: /data
|
||||
{{- if .Values.tls.enabled }}
|
||||
- name: tls
|
||||
mountPath: {{ .Values.tls.certPath | default "/data/cert" }}
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
resources:
|
||||
{{ toYaml .Values.resources | indent 12 }}
|
||||
{{- with .Values.podSecurityContext }}
|
||||
securityContext:
|
||||
{{ toYaml . | indent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{ toYaml . | indent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.affinity }}
|
||||
affinity:
|
||||
{{ toYaml . | indent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.tolerations }}
|
||||
tolerations:
|
||||
{{ toYaml . | indent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
- name: data
|
||||
emptyDir: {}
|
||||
{{- if .Values.tls.enabled }}
|
||||
- name: tls
|
||||
secret:
|
||||
secretName: {{ template "podinfo.tlsSecretName" . }}
|
||||
{{- end }}
|
||||
{{- with .Values.topologySpreadConstraints }}
|
||||
topologySpreadConstraints:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
@@ -1,42 +0,0 @@
|
||||
{{- if .Values.grpcRoute.enabled -}}
|
||||
{{- $fullName := include "podinfo.fullname" . -}}
|
||||
{{- $grpcPort := .Values.service.grpcPort -}}
|
||||
apiVersion: gateway.networking.k8s.io/v1
|
||||
kind: GRPCRoute
|
||||
metadata:
|
||||
name: {{ $fullName }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.grpcRoute.additionalLabels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.grpcRoute.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
parentRefs:
|
||||
{{- with .Values.grpcRoute.parentRefs }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.grpcRoute.hostnames }}
|
||||
hostnames:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
rules:
|
||||
{{- range .Values.grpcRoute.rules }}
|
||||
- backendRefs:
|
||||
- name: {{ $fullName }}
|
||||
port: {{ $grpcPort }}
|
||||
weight: 1
|
||||
{{- with .matches }}
|
||||
matches:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .filters }}
|
||||
filters:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,37 +0,0 @@
|
||||
{{- $hooks := dict "preInstall" "pre-install" "postInstall" "post-install" "preDelete" "pre-delete" "postDelete" "post-delete" "preUpgrade" "pre-upgrade" "postUpgrade" "post-upgrade" "preRollback" "pre-rollback" "postRollback" "post-rollback" }}
|
||||
{{- range $hookName, $hookType := $hooks }}
|
||||
{{- $hookConfig := index $.Values.hooks $hookName }}
|
||||
{{- if and $hookConfig $hookConfig.job $hookConfig.job.enabled }}
|
||||
---
|
||||
apiVersion: batch/v1
|
||||
kind: Job
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" $ }}-{{ $hookType }}
|
||||
namespace: {{ include "podinfo.namespace" $ }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" $ | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": {{ $hookType }}
|
||||
"helm.sh/hook-delete-policy": {{ $hookConfig.job.hookDeletePolicy }}
|
||||
spec:
|
||||
{{- if kindIs "float64" $hookConfig.job.ttlSecondsAfterFinished }}
|
||||
ttlSecondsAfterFinished: {{ $hookConfig.job.ttlSecondsAfterFinished | int }}
|
||||
{{- end }}
|
||||
template:
|
||||
spec:
|
||||
containers:
|
||||
- name: job
|
||||
image: "{{ $.Values.image.repository }}:{{ $.Values.image.tag }}"
|
||||
imagePullPolicy: {{ $.Values.image.pullPolicy }}
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
{{- if kindIs "float64" $hookConfig.job.sleepSeconds }}
|
||||
sleep {{ $hookConfig.job.sleepSeconds | int }}
|
||||
{{- end }}
|
||||
exit {{ $hookConfig.job.exitCode | default 0 }}
|
||||
restartPolicy: Never
|
||||
backoffLimit: 1
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,42 +0,0 @@
|
||||
{{- if .Values.hpa.enabled -}}
|
||||
apiVersion: autoscaling/v2
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
minReplicas: {{ .Values.replicaCount }}
|
||||
maxReplicas: {{ .Values.hpa.maxReplicas }}
|
||||
metrics:
|
||||
{{- if .Values.hpa.cpu }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: {{ .Values.hpa.cpu }}
|
||||
{{- end }}
|
||||
{{- if .Values.hpa.memory }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: memory
|
||||
target:
|
||||
type: AverageValue
|
||||
averageValue: {{ .Values.hpa.memory }}
|
||||
{{- end }}
|
||||
{{- if .Values.hpa.requests }}
|
||||
- type: Pods
|
||||
pods:
|
||||
metric:
|
||||
name: http_requests
|
||||
target:
|
||||
type: AverageValue
|
||||
averageValue: {{ .Values.hpa.requests }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,42 +0,0 @@
|
||||
{{- if .Values.httpRoute.enabled -}}
|
||||
{{- $fullName := include "podinfo.fullname" . -}}
|
||||
{{- $svcPort := .Values.service.externalPort -}}
|
||||
apiVersion: gateway.networking.k8s.io/v1
|
||||
kind: HTTPRoute
|
||||
metadata:
|
||||
name: {{ $fullName }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.httpRoute.additionalLabels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.httpRoute.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
parentRefs:
|
||||
{{- with .Values.httpRoute.parentRefs }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.httpRoute.hostnames }}
|
||||
hostnames:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
rules:
|
||||
{{- range .Values.httpRoute.rules }}
|
||||
{{- with .matches }}
|
||||
- matches:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .filters }}
|
||||
filters:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
backendRefs:
|
||||
- name: {{ $fullName }}
|
||||
port: {{ $svcPort }}
|
||||
weight: 1
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,45 +0,0 @@
|
||||
{{- if .Values.ingress.enabled -}}
|
||||
{{- $fullName := include "podinfo.fullname" . -}}
|
||||
{{- $svcPort := .Values.service.externalPort -}}
|
||||
apiVersion: networking.k8s.io/v1
|
||||
kind: Ingress
|
||||
metadata:
|
||||
name: {{ $fullName }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.ingress.additionalLabels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.ingress.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
ingressClassName: {{ .Values.ingress.className }}
|
||||
{{- if .Values.ingress.tls }}
|
||||
tls:
|
||||
{{- range .Values.ingress.tls }}
|
||||
- hosts:
|
||||
{{- range .hosts }}
|
||||
- {{ . | quote }}
|
||||
{{- end }}
|
||||
secretName: {{ .secretName }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
rules:
|
||||
{{- range .Values.ingress.hosts }}
|
||||
- host: {{ .host | quote }}
|
||||
http:
|
||||
paths:
|
||||
{{- range .paths }}
|
||||
- path: {{ .path }}
|
||||
pathType: {{ .pathType }}
|
||||
backend:
|
||||
service:
|
||||
name: {{ $fullName }}
|
||||
port:
|
||||
number: {{ $svcPort }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,14 +0,0 @@
|
||||
{{- if and .Values.podDisruptionBudget (gt (int .Values.replicaCount) 1) }}
|
||||
apiVersion: policy/v1
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: {{ include "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
{{- include "podinfo.selectorLabels" . | nindent 6 }}
|
||||
{{- toYaml .Values.podDisruptionBudget | nindent 2 }}
|
||||
{{- end }}
|
||||
@@ -1,12 +0,0 @@
|
||||
{{- if .Values.redis.enabled -}}
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-redis
|
||||
data:
|
||||
redis.conf: |
|
||||
maxmemory 64mb
|
||||
maxmemory-policy allkeys-lru
|
||||
save ""
|
||||
appendonly no
|
||||
{{- end }}
|
||||
@@ -1,71 +0,0 @@
|
||||
{{- if .Values.redis.enabled -}}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-redis
|
||||
labels:
|
||||
app: {{ template "podinfo.fullname" . }}-redis
|
||||
spec:
|
||||
strategy:
|
||||
type: Recreate
|
||||
selector:
|
||||
matchLabels:
|
||||
app: {{ template "podinfo.fullname" . }}-redis
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app: {{ template "podinfo.fullname" . }}-redis
|
||||
annotations:
|
||||
checksum/config: {{ include (print $.Template.BasePath "/redis/config.yaml") . | sha256sum | quote }}
|
||||
spec:
|
||||
{{- if .Values.serviceAccount.enabled }}
|
||||
serviceAccountName: {{ template "podinfo.serviceAccountName" . }}
|
||||
{{- end }}
|
||||
{{- if .Values.redis.imagePullSecrets }}
|
||||
imagePullSecrets: {{ toYaml .Values.redis.imagePullSecrets | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: redis
|
||||
image: "{{ .Values.redis.repository }}:{{ .Values.redis.tag }}"
|
||||
imagePullPolicy: IfNotPresent
|
||||
command:
|
||||
- redis-server
|
||||
- "/redis-master/redis.conf"
|
||||
ports:
|
||||
- name: redis
|
||||
containerPort: 6379
|
||||
protocol: TCP
|
||||
livenessProbe:
|
||||
tcpSocket:
|
||||
port: redis
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- redis-cli
|
||||
- ping
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 128Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
volumeMounts:
|
||||
- mountPath: /var/lib/redis
|
||||
name: data
|
||||
- mountPath: /redis-master
|
||||
name: config
|
||||
volumes:
|
||||
- name: data
|
||||
emptyDir: {}
|
||||
- name: config
|
||||
configMap:
|
||||
name: {{ template "podinfo.fullname" . }}-redis
|
||||
items:
|
||||
- key: redis.conf
|
||||
path: redis.conf
|
||||
{{- end }}
|
||||
@@ -1,18 +0,0 @@
|
||||
{{- if .Values.redis.enabled -}}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-redis
|
||||
labels:
|
||||
app: {{ template "podinfo.fullname" . }}-redis
|
||||
spec:
|
||||
type: ClusterIP
|
||||
selector:
|
||||
app: {{ template "podinfo.fullname" . }}-redis
|
||||
ports:
|
||||
- name: redis
|
||||
port: 6379
|
||||
protocol: TCP
|
||||
targetPort: redis
|
||||
appProtocol: redis
|
||||
{{- end }}
|
||||
@@ -1,46 +0,0 @@
|
||||
{{- if .Values.service.enabled -}}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.service.additionalLabels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.service.annotations }}
|
||||
annotations:
|
||||
{{ toYaml . | indent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
type: {{ .Values.service.type }}
|
||||
ports:
|
||||
- port: {{ .Values.service.externalPort }}
|
||||
targetPort: http
|
||||
protocol: TCP
|
||||
name: http
|
||||
{{- if (and (eq .Values.service.type "NodePort") (not (empty .Values.service.nodePort))) }}
|
||||
nodePort: {{ .Values.service.nodePort }}
|
||||
{{- end }}
|
||||
{{- if .Values.tls.enabled }}
|
||||
- port: {{ .Values.tls.port | default 9899 }}
|
||||
targetPort: https
|
||||
protocol: TCP
|
||||
name: https
|
||||
{{- end }}
|
||||
{{- if .Values.service.grpcPort }}
|
||||
- port: {{ .Values.service.grpcPort }}
|
||||
targetPort: grpc
|
||||
protocol: TCP
|
||||
name: grpc
|
||||
{{- end }}
|
||||
selector:
|
||||
{{- include "podinfo.selectorLabels" . | nindent 4 }}
|
||||
{{- if .Values.service.trafficDistribution }}
|
||||
trafficDistribution: {{ .Values.service.trafficDistribution }}
|
||||
{{- end }}
|
||||
{{- if ( and (.Values.service.externalTrafficPolicy) (eq .Values.service.type "LoadBalancer") ) }}
|
||||
externalTrafficPolicy: {{ .Values.service.externalTrafficPolicy }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,12 +0,0 @@
|
||||
{{- if .Values.serviceAccount.enabled -}}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ template "podinfo.serviceAccountName" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.serviceAccount.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 2 }}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
@@ -1,23 +0,0 @@
|
||||
{{- if .Values.serviceMonitor.enabled -}}
|
||||
apiVersion: monitoring.coreos.com/v1
|
||||
kind: ServiceMonitor
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
{{- with .Values.serviceMonitor.additionalLabels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
endpoints:
|
||||
- path: /metrics
|
||||
port: http
|
||||
interval: {{ .Values.serviceMonitor.interval }}
|
||||
namespaceSelector:
|
||||
matchNames:
|
||||
- {{ include "podinfo.namespace" . }}
|
||||
selector:
|
||||
matchLabels:
|
||||
{{- include "podinfo.selectorLabels" . | nindent 6 }}
|
||||
{{- end }}
|
||||
@@ -1,30 +0,0 @@
|
||||
{{- if .Values.cache }}
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-cache-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: curl
|
||||
image: curlimages/curl:7.69.0
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
curl -sd 'data' ${PODINFO_SVC}/cache/test &&
|
||||
curl -s ${PODINFO_SVC}/cache/test | grep data &&
|
||||
curl -s -XDELETE ${PODINFO_SVC}/cache/test
|
||||
env:
|
||||
- name: PODINFO_SVC
|
||||
value: "{{ template "podinfo.fullname" . }}.{{ include "podinfo.namespace" . }}:{{ .Values.service.externalPort }}"
|
||||
restartPolicy: Never
|
||||
{{- end }}
|
||||
@@ -1,22 +0,0 @@
|
||||
{{- if .Values.faults.testFail }}
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-fault-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: fault
|
||||
image: alpine:3.11
|
||||
command: ['/bin/sh']
|
||||
args: ['-c', 'exit 1']
|
||||
restartPolicy: Never
|
||||
{{- end }}
|
||||
@@ -1,20 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-grpc-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: grpc-health-probe
|
||||
image: stefanprodan/grpc_health_probe:v0.3.0
|
||||
command: ['grpc_health_probe']
|
||||
args: ['-addr={{ template "podinfo.fullname" . }}.{{ include "podinfo.namespace" . }}:{{ .Values.service.grpcPort }}']
|
||||
restartPolicy: Never
|
||||
@@ -1,27 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-jwt-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: tools
|
||||
image: giantswarm/tiny-tools
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
TOKEN=$(curl -sd 'test' ${PODINFO_SVC}/token | jq -r .token) &&
|
||||
curl -sH "Authorization: Bearer ${TOKEN}" ${PODINFO_SVC}/token/validate | grep test
|
||||
env:
|
||||
- name: PODINFO_SVC
|
||||
value: "{{ template "podinfo.fullname" . }}.{{ include "podinfo.namespace" . }}:{{ .Values.service.externalPort }}"
|
||||
restartPolicy: Never
|
||||
@@ -1,26 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-service-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: curl
|
||||
image: curlimages/curl:7.69.0
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
curl -s ${PODINFO_SVC}/api/info | grep version
|
||||
env:
|
||||
- name: PODINFO_SVC
|
||||
value: "{{ template "podinfo.fullname" . }}.{{ include "podinfo.namespace" . }}:{{ .Values.service.externalPort }}"
|
||||
restartPolicy: Never
|
||||
@@ -1,22 +0,0 @@
|
||||
{{- if .Values.faults.testTimeout }}
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-fault-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: fault
|
||||
image: alpine:3.11
|
||||
command: ['/bin/sh']
|
||||
args: ['-c', 'while sleep 3600; do :; done']
|
||||
restartPolicy: Never
|
||||
{{- end }}
|
||||
@@ -1,28 +0,0 @@
|
||||
{{- if .Values.tls.enabled -}}
|
||||
apiVersion: v1
|
||||
kind: Pod
|
||||
metadata:
|
||||
name: {{ template "podinfo.fullname" . }}-tls-test-{{ randAlphaNum 5 | lower }}
|
||||
namespace: {{ include "podinfo.namespace" . }}
|
||||
labels:
|
||||
{{- include "podinfo.labels" . | nindent 4 }}
|
||||
annotations:
|
||||
"helm.sh/hook": test-success
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
sidecar.istio.io/inject: "false"
|
||||
linkerd.io/inject: disabled
|
||||
appmesh.k8s.aws/sidecarInjectorWebhook: disabled
|
||||
spec:
|
||||
containers:
|
||||
- name: curl
|
||||
image: curlimages/curl:7.69.0
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
curl -sk ${PODINFO_SVC}/api/info | grep version
|
||||
env:
|
||||
- name: PODINFO_SVC
|
||||
value: "https://{{ template "podinfo.fullname" . }}.{{ include "podinfo.namespace" . }}:{{ .Values.tls.port }}"
|
||||
restartPolicy: Never
|
||||
{{- end }}
|
||||
@@ -1,210 +0,0 @@
|
||||
# Production values for podinfo.
|
||||
# Includes Redis deployment and memory limits.
|
||||
|
||||
replicaCount: 1
|
||||
logLevel: info
|
||||
backend: #http://backend-podinfo:9898/echo
|
||||
backends: []
|
||||
|
||||
image:
|
||||
repository: ghcr.io/stefanprodan/podinfo
|
||||
tag: 6.11.0
|
||||
pullPolicy: IfNotPresent
|
||||
|
||||
ui:
|
||||
color: "#34577c"
|
||||
message: ""
|
||||
logo: ""
|
||||
|
||||
# failure conditions
|
||||
faults:
|
||||
delay: false
|
||||
error: false
|
||||
unhealthy: false
|
||||
unready: false
|
||||
testFail: false
|
||||
testTimeout: false
|
||||
|
||||
# Kubernetes Service settings
|
||||
service:
|
||||
enabled: true
|
||||
annotations: {}
|
||||
additionalLabels: { }
|
||||
type: ClusterIP
|
||||
metricsPort: 9797
|
||||
httpPort: 9898
|
||||
externalPort: 9898
|
||||
grpcPort: 9999
|
||||
grpcService: podinfo
|
||||
nodePort: 31198
|
||||
trafficDistribution: ""
|
||||
externalTrafficPolicy: ""
|
||||
|
||||
# enable h2c protocol (non-TLS version of HTTP/2)
|
||||
h2c:
|
||||
enabled: false
|
||||
|
||||
# config file settings
|
||||
config:
|
||||
# config file path
|
||||
path: ""
|
||||
# config file name
|
||||
name: ""
|
||||
|
||||
# Additional command line arguments to pass to podinfo container
|
||||
extraArgs: []
|
||||
|
||||
# enable tls on the podinfo service
|
||||
tls:
|
||||
enabled: false
|
||||
# the name of the secret used to mount the certificate key pair
|
||||
secretName:
|
||||
# the path where the certificate key pair will be mounted
|
||||
certPath: /data/cert
|
||||
# the port used to host the tls endpoint on the service
|
||||
port: 9899
|
||||
# the port used to bind the tls port to the host
|
||||
# NOTE: requires privileged container with NET_BIND_SERVICE capability -- this is useful for testing
|
||||
# in local clusters such as kind without port forwarding
|
||||
hostPort:
|
||||
|
||||
# create a certificate manager certificate (cert-manager required)
|
||||
certificate:
|
||||
create: false
|
||||
# the issuer used to issue the certificate
|
||||
issuerRef:
|
||||
kind: ClusterIssuer
|
||||
name: self-signed
|
||||
# the hostname / subject alternative names for the certificate
|
||||
dnsNames:
|
||||
- podinfo
|
||||
|
||||
# metrics-server add-on required
|
||||
hpa:
|
||||
enabled: true
|
||||
maxReplicas: 5
|
||||
# average total CPU usage per pod (1-100)
|
||||
cpu: 99
|
||||
# average memory usage per pod (100Mi-1Gi)
|
||||
memory:
|
||||
# average http requests per second per pod (k8s-prometheus-adapter)
|
||||
requests:
|
||||
|
||||
# Redis address in the format tcp://<host>:<port>
|
||||
cache: ""
|
||||
# Redis deployment
|
||||
redis:
|
||||
enabled: true
|
||||
repository: redis
|
||||
tag: 8.6.1
|
||||
|
||||
serviceAccount:
|
||||
# Specifies whether a service account should be created
|
||||
enabled: false
|
||||
# The name of the service account to use.
|
||||
# If not set and create is true, a name is generated using the fullname template
|
||||
name:
|
||||
# List of image pull secrets if pulling from private registries
|
||||
imagePullSecrets: []
|
||||
|
||||
# set container security context
|
||||
securityContext: {}
|
||||
|
||||
# set pod security context
|
||||
podSecurityContext: {}
|
||||
|
||||
# -- Expose the service via Kubernetes Ingress
|
||||
# Requires an Ingress controller
|
||||
# Docs https://kubernetes.io/docs/concepts/services-networking/ingress/
|
||||
ingress:
|
||||
enabled: false
|
||||
className: ""
|
||||
additionalLabels: {}
|
||||
annotations: {}
|
||||
# kubernetes.io/ingress.class: nginx
|
||||
# kubernetes.io/tls-acme: "true"
|
||||
hosts:
|
||||
- host: podinfo.local
|
||||
paths:
|
||||
- path: /
|
||||
pathType: ImplementationSpecific
|
||||
tls: []
|
||||
# - secretName: chart-example-tls
|
||||
# hosts:
|
||||
# - chart-example.local
|
||||
|
||||
# -- Expose the service via Gateway HTTPRoute
|
||||
# Requires a Gateway controller
|
||||
# Docs https://gateway-api.sigs.k8s.io/guides/
|
||||
httpRoute:
|
||||
# HTTPRoute enabled.
|
||||
enabled: false
|
||||
# Add additional labels to the HTTPRoute.
|
||||
additionalLabels: {}
|
||||
# HTTPRoute annotations.
|
||||
annotations: {}
|
||||
# Which Gateways this Route is attached to.
|
||||
parentRefs:
|
||||
- name: gateway
|
||||
sectionName: http
|
||||
# namespace: default
|
||||
# Hostnames matching HTTP header.
|
||||
hostnames:
|
||||
- podinfo.local
|
||||
# List of rules and filters applied.
|
||||
rules:
|
||||
- matches:
|
||||
- path:
|
||||
type: PathPrefix
|
||||
value: /
|
||||
|
||||
# create Prometheus Operator monitor
|
||||
serviceMonitor:
|
||||
enabled: false
|
||||
interval: 15s
|
||||
additionalLabels: {}
|
||||
|
||||
resources:
|
||||
limits:
|
||||
memory: 256Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 64Mi
|
||||
|
||||
# Extra environment variables for the podinfo container
|
||||
extraEnvs: []
|
||||
# Example on how to configure extraEnvs
|
||||
# - name: OTEL_EXPORTER_OTLP_TRACES_ENDPOINT
|
||||
# value: "http://otel:4317"
|
||||
# - name: MULTIPLE_VALUES
|
||||
# value: TEST
|
||||
|
||||
nodeSelector: {}
|
||||
|
||||
tolerations: []
|
||||
|
||||
affinity: {}
|
||||
|
||||
podAnnotations: {}
|
||||
|
||||
# https://kubernetes.io/docs/concepts/workloads/pods/pod-lifecycle#container-probes
|
||||
probes:
|
||||
readiness:
|
||||
initialDelaySeconds: 1
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 3
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
liveness:
|
||||
initialDelaySeconds: 1
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 3
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
startup:
|
||||
enable: false
|
||||
initialDelaySeconds: 10
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 20
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
@@ -1,304 +0,0 @@
|
||||
# Default values for podinfo.
|
||||
|
||||
replicaCount: 1
|
||||
logLevel: info
|
||||
host: #0.0.0.0
|
||||
backend: #http://backend-podinfo:9898/echo
|
||||
backends: []
|
||||
|
||||
image:
|
||||
repository: ghcr.io/stefanprodan/podinfo
|
||||
tag: 6.11.0
|
||||
pullPolicy: IfNotPresent
|
||||
pullSecrets: []
|
||||
|
||||
ui:
|
||||
color: "#34577c"
|
||||
message: ""
|
||||
logo: ""
|
||||
|
||||
# failure conditions
|
||||
faults:
|
||||
delay: false
|
||||
error: false
|
||||
unhealthy: false
|
||||
unready: false
|
||||
testFail: false
|
||||
testTimeout: false
|
||||
|
||||
# Kubernetes Service settings
|
||||
service:
|
||||
enabled: true
|
||||
annotations: {}
|
||||
additionalLabels: { }
|
||||
type: ClusterIP
|
||||
metricsPort: 9797
|
||||
httpPort: 9898
|
||||
externalPort: 9898
|
||||
grpcPort: 9999
|
||||
grpcService: podinfo
|
||||
nodePort: 31198
|
||||
# the port used to bind the http port to the host
|
||||
# NOTE: requires privileged container with NET_BIND_SERVICE capability -- this is useful for testing
|
||||
# in local clusters such as kind without port forwarding
|
||||
hostPort:
|
||||
# Stable from Kubernetes v1.33+ with a value of PreferClose. Additional values are PreferSameZone and PreferSameNode from v1.34+. Empty string means it's disabled.
|
||||
trafficDistribution: ""
|
||||
externalTrafficPolicy: ""
|
||||
|
||||
# enable h2c protocol (non-TLS version of HTTP/2)
|
||||
h2c:
|
||||
enabled: false
|
||||
|
||||
# config file settings
|
||||
config:
|
||||
# config file path
|
||||
path: ""
|
||||
# config file name
|
||||
name: ""
|
||||
|
||||
# Additional command line arguments to pass to podinfo container
|
||||
extraArgs: []
|
||||
|
||||
# Extra environment variables for the podinfo container
|
||||
extraEnvs: []
|
||||
# Example on how to configure extraEnvs
|
||||
# - name: OTEL_EXPORTER_OTLP_TRACES_ENDPOINT
|
||||
# value: "http://otel:4317"
|
||||
# - name: MULTIPLE_VALUES
|
||||
# value: TEST
|
||||
|
||||
# enable tls on the podinfo service
|
||||
tls:
|
||||
enabled: false
|
||||
# the name of the secret used to mount the certificate key pair
|
||||
secretName:
|
||||
# the path where the certificate key pair will be mounted
|
||||
certPath: /data/cert
|
||||
# the port used to host the tls endpoint on the service
|
||||
port: 9899
|
||||
# the port used to bind the tls port to the host
|
||||
# NOTE: requires privileged container with NET_BIND_SERVICE capability -- this is useful for testing
|
||||
# in local clusters such as kind without port forwarding
|
||||
hostPort:
|
||||
|
||||
# create a certificate manager certificate (cert-manager required)
|
||||
certificate:
|
||||
create: false
|
||||
# the issuer used to issue the certificate
|
||||
issuerRef:
|
||||
kind: ClusterIssuer
|
||||
name: self-signed
|
||||
# the hostname / subject alternative names for the certificate
|
||||
dnsNames:
|
||||
- podinfo
|
||||
|
||||
# Helm hooks (for testing purposes)
|
||||
hooks:
|
||||
preInstall:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
postInstall:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
preDelete:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
postDelete:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
preUpgrade:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
postUpgrade:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
preRollback:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
postRollback:
|
||||
job:
|
||||
enabled: false
|
||||
hookDeletePolicy: hook-succeeded,hook-failed
|
||||
ttlSecondsAfterFinished:
|
||||
sleepSeconds:
|
||||
exitCode: 0
|
||||
|
||||
# metrics-server add-on required
|
||||
hpa:
|
||||
enabled: false
|
||||
maxReplicas: 10
|
||||
# average total CPU usage per pod (1-100)
|
||||
cpu:
|
||||
# average memory usage per pod (100Mi-1Gi)
|
||||
memory:
|
||||
# average http requests per second per pod (k8s-prometheus-adapter)
|
||||
requests:
|
||||
|
||||
# Redis address in the format tcp://<host>:<port>
|
||||
cache: ""
|
||||
# Redis deployment
|
||||
redis:
|
||||
enabled: false
|
||||
repository: docker.io/redis
|
||||
tag: 8.6.1
|
||||
imagePullSecrets: []
|
||||
|
||||
serviceAccount:
|
||||
# Specifies whether a service account should be created
|
||||
enabled: false
|
||||
# The name of the service account to use.
|
||||
# If not set and create is true, a name is generated using the fullname template
|
||||
name:
|
||||
# List of image pull secrets if pulling from private registries
|
||||
imagePullSecrets: []
|
||||
|
||||
# set container security context
|
||||
securityContext: {}
|
||||
|
||||
# set pod security context
|
||||
podSecurityContext: {}
|
||||
|
||||
# -- Expose the service via Kubernetes Ingress
|
||||
# Requires an Ingress controller
|
||||
# Docs https://kubernetes.io/docs/concepts/services-networking/ingress/
|
||||
ingress:
|
||||
enabled: false
|
||||
className: ""
|
||||
additionalLabels: {}
|
||||
annotations: {}
|
||||
# kubernetes.io/ingress.class: nginx
|
||||
# kubernetes.io/tls-acme: "true"
|
||||
hosts:
|
||||
- host: podinfo.local
|
||||
paths:
|
||||
- path: /
|
||||
pathType: ImplementationSpecific
|
||||
tls: []
|
||||
# - secretName: chart-example-tls
|
||||
# hosts:
|
||||
# - chart-example.local
|
||||
|
||||
# -- Expose the service via Gateway HTTPRoute
|
||||
# Requires a Gateway controller
|
||||
# Docs https://gateway-api.sigs.k8s.io/guides/
|
||||
httpRoute:
|
||||
# HTTPRoute enabled.
|
||||
enabled: false
|
||||
# Add additional labels to the HTTPRoute.
|
||||
additionalLabels: {}
|
||||
# HTTPRoute annotations.
|
||||
annotations: {}
|
||||
# Which Gateways this Route is attached to.
|
||||
parentRefs:
|
||||
- name: gateway
|
||||
sectionName: http
|
||||
# namespace: default
|
||||
# Hostnames matching HTTP header.
|
||||
hostnames:
|
||||
- podinfo.local
|
||||
# List of rules and filters applied.
|
||||
rules:
|
||||
- matches:
|
||||
- path:
|
||||
type: PathPrefix
|
||||
value: /
|
||||
|
||||
# -- Expose the gRPC service via Gateway GRPCRoute
|
||||
# Requires a Gateway controller with GRPCRoute support
|
||||
# Docs https://gateway-api.sigs.k8s.io/guides/grpc-routing/
|
||||
grpcRoute:
|
||||
# GRPCRoute enabled.
|
||||
enabled: false
|
||||
# Add additional labels to the GRPCRoute.
|
||||
additionalLabels: {}
|
||||
# GRPCRoute annotations.
|
||||
annotations: {}
|
||||
# Which Gateways this Route is attached to.
|
||||
parentRefs:
|
||||
- name: gateway
|
||||
sectionName: http
|
||||
# namespace: default
|
||||
# Hostnames matching HTTP header.
|
||||
hostnames:
|
||||
- podinfo.local
|
||||
# List of rules applied.
|
||||
rules:
|
||||
- {}
|
||||
|
||||
# create Prometheus Operator monitor
|
||||
serviceMonitor:
|
||||
enabled: false
|
||||
interval: 15s
|
||||
additionalLabels: {}
|
||||
|
||||
resources:
|
||||
limits:
|
||||
requests:
|
||||
cpu: 1m
|
||||
memory: 16Mi
|
||||
|
||||
nodeSelector: {}
|
||||
|
||||
tolerations: []
|
||||
|
||||
affinity: {}
|
||||
|
||||
podAnnotations: {}
|
||||
|
||||
# https://kubernetes.io/docs/concepts/workloads/pods/pod-topology-spread-constraints/
|
||||
topologySpreadConstraints: []
|
||||
|
||||
# Disruption budget will be configured only when the replicaCount is greater than 1
|
||||
podDisruptionBudget: {}
|
||||
# maxUnavailable: 1
|
||||
|
||||
# https://kubernetes.io/docs/concepts/workloads/pods/pod-lifecycle#container-probes
|
||||
probes:
|
||||
readiness:
|
||||
initialDelaySeconds: 1
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 3
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
liveness:
|
||||
initialDelaySeconds: 1
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 3
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
startup:
|
||||
enable: false
|
||||
initialDelaySeconds: 10
|
||||
timeoutSeconds: 5
|
||||
failureThreshold: 20
|
||||
successThreshold: 1
|
||||
periodSeconds: 10
|
||||
@@ -1,403 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"bytes"
|
||||
"context"
|
||||
"crypto/tls"
|
||||
"fmt"
|
||||
"net"
|
||||
"net/http"
|
||||
"net/url"
|
||||
"os"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/gorilla/websocket"
|
||||
"github.com/spf13/cobra"
|
||||
"go.uber.org/zap"
|
||||
"google.golang.org/grpc"
|
||||
"google.golang.org/grpc/codes"
|
||||
"google.golang.org/grpc/credentials"
|
||||
"google.golang.org/grpc/credentials/insecure"
|
||||
"google.golang.org/grpc/health/grpc_health_v1"
|
||||
"google.golang.org/grpc/status"
|
||||
)
|
||||
|
||||
var (
|
||||
retryCount int
|
||||
retryDelay time.Duration
|
||||
method string
|
||||
body string
|
||||
timeout time.Duration
|
||||
grpcServiceName string
|
||||
grpcTLS bool
|
||||
)
|
||||
|
||||
var checkCmd = &cobra.Command{
|
||||
Use: `check`,
|
||||
Short: "Health check commands",
|
||||
Long: "Commands for running health checks",
|
||||
}
|
||||
|
||||
var checkUrlCmd = &cobra.Command{
|
||||
Use: `http [address]`,
|
||||
Short: "HTTP(S) health check",
|
||||
Example: ` check http https://httpbin.org/anything --method=POST --retry=2 --delay=2s --timeout=3s --body='{"test"=1}'`,
|
||||
RunE: runCheck,
|
||||
}
|
||||
|
||||
var checkTcpCmd = &cobra.Command{
|
||||
Use: `tcp [address]`,
|
||||
Short: "TCP health check",
|
||||
Example: ` check tcp httpbin.org:443 --retry=1 --delay=2s --timeout=2s`,
|
||||
RunE: runCheckTCP,
|
||||
}
|
||||
|
||||
var checkCertCmd = &cobra.Command{
|
||||
Use: `cert [address]`,
|
||||
Short: "SSL/TLS certificate validity check",
|
||||
Example: ` check cert httpbin.org`,
|
||||
RunE: runCheckCert,
|
||||
}
|
||||
|
||||
var checkgRPCCmd = &cobra.Command{
|
||||
Use: `grpc [address]`,
|
||||
Short: "gRPC health check",
|
||||
Example: ` check grpc localhost:8080 --service=podinfo --retry=1 --delay=2s --timeout=2s`,
|
||||
RunE: runCheckgPRC,
|
||||
}
|
||||
|
||||
var checkWsCmd = &cobra.Command{
|
||||
Use: `ws [address]`,
|
||||
Short: "WebSocket round-trip health check",
|
||||
Example: ` check ws ws://localhost:9898/ws/echo --retry=1 --delay=2s --timeout=5s`,
|
||||
RunE: runCheckWs,
|
||||
}
|
||||
|
||||
func init() {
|
||||
checkUrlCmd.Flags().StringVar(&method, "method", "GET", "HTTP method")
|
||||
checkUrlCmd.Flags().StringVar(&body, "body", "", "HTTP POST/PUT content")
|
||||
checkUrlCmd.Flags().IntVar(&retryCount, "retry", 0, "times to retry the HTTP call")
|
||||
checkUrlCmd.Flags().DurationVar(&retryDelay, "delay", 1*time.Second, "wait duration between retries")
|
||||
checkUrlCmd.Flags().DurationVar(&timeout, "timeout", 5*time.Second, "timeout")
|
||||
checkCmd.AddCommand(checkUrlCmd)
|
||||
|
||||
checkTcpCmd.Flags().IntVar(&retryCount, "retry", 0, "times to retry the TCP check")
|
||||
checkTcpCmd.Flags().DurationVar(&retryDelay, "delay", 1*time.Second, "wait duration between retries")
|
||||
checkTcpCmd.Flags().DurationVar(&timeout, "timeout", 5*time.Second, "timeout")
|
||||
checkCmd.AddCommand(checkTcpCmd)
|
||||
|
||||
checkgRPCCmd.Flags().IntVar(&retryCount, "retry", 0, "times to retry the TCP check")
|
||||
checkgRPCCmd.Flags().DurationVar(&retryDelay, "delay", 1*time.Second, "wait duration between retries")
|
||||
checkgRPCCmd.Flags().DurationVar(&timeout, "timeout", 5*time.Second, "timeout")
|
||||
checkgRPCCmd.Flags().StringVar(&grpcServiceName, "service", "", "gRPC service name")
|
||||
checkgRPCCmd.Flags().BoolVar(&grpcTLS, "tls", false, "use TLS for gRPC connection")
|
||||
checkCmd.AddCommand(checkgRPCCmd)
|
||||
|
||||
checkCmd.AddCommand(checkCertCmd)
|
||||
|
||||
checkWsCmd.Flags().IntVar(&retryCount, "retry", 0, "times to retry the WebSocket check")
|
||||
checkWsCmd.Flags().DurationVar(&retryDelay, "delay", 1*time.Second, "wait duration between retries")
|
||||
checkWsCmd.Flags().DurationVar(&timeout, "timeout", 5*time.Second, "timeout")
|
||||
checkCmd.AddCommand(checkWsCmd)
|
||||
|
||||
rootCmd.AddCommand(checkCmd)
|
||||
}
|
||||
|
||||
func runCheck(cmd *cobra.Command, args []string) error {
|
||||
if retryCount < 0 {
|
||||
return fmt.Errorf("--retry is required")
|
||||
}
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required! example: check http https://httpbin.org")
|
||||
}
|
||||
|
||||
address := args[0]
|
||||
if !strings.HasPrefix(address, "http://") && !strings.HasPrefix(address, "https://") {
|
||||
address = fmt.Sprintf("http://%s", address)
|
||||
}
|
||||
|
||||
for n := 0; n <= retryCount; n++ {
|
||||
if n != 1 {
|
||||
time.Sleep(retryDelay)
|
||||
}
|
||||
|
||||
req, err := http.NewRequest(method, address, bytes.NewBuffer([]byte(body)))
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
ctx, cancel := context.WithTimeout(req.Context(), timeout)
|
||||
resp, err := http.DefaultClient.Do(req.WithContext(ctx))
|
||||
cancel()
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
|
||||
if resp.Body != nil {
|
||||
resp.Body.Close()
|
||||
}
|
||||
|
||||
if resp.StatusCode >= 200 && resp.StatusCode < 400 {
|
||||
logger.Info("check succeed",
|
||||
zap.String("address", address),
|
||||
zap.Int("status code", resp.StatusCode),
|
||||
zap.String("response size", fmtContentLength(resp.ContentLength)))
|
||||
os.Exit(0)
|
||||
} else {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Int("status code", resp.StatusCode))
|
||||
continue
|
||||
}
|
||||
}
|
||||
|
||||
os.Exit(1)
|
||||
return nil
|
||||
}
|
||||
|
||||
func runCheckTCP(cmd *cobra.Command, args []string) error {
|
||||
if retryCount < 0 {
|
||||
return fmt.Errorf("--retry is required")
|
||||
}
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required! example: check tcp httpbin.org:80")
|
||||
}
|
||||
address := args[0]
|
||||
|
||||
for n := 0; n <= retryCount; n++ {
|
||||
if n != 1 {
|
||||
time.Sleep(retryDelay)
|
||||
}
|
||||
|
||||
conn, err := net.DialTimeout("tcp", address, timeout)
|
||||
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
|
||||
conn.Close()
|
||||
logger.Info("check succeed", zap.String("address", address))
|
||||
os.Exit(0)
|
||||
|
||||
}
|
||||
|
||||
os.Exit(1)
|
||||
return nil
|
||||
}
|
||||
|
||||
func runCheckCert(cmd *cobra.Command, args []string) error {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required! example: check cert httpbin.org")
|
||||
}
|
||||
host := args[0]
|
||||
if !strings.HasPrefix(host, "https://") {
|
||||
host = "https://" + host
|
||||
}
|
||||
|
||||
u, err := url.Parse(host)
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", host),
|
||||
zap.Error(err))
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
address := u.Hostname() + ":443"
|
||||
ipConn, err := net.DialTimeout("tcp", address, 5*time.Second)
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
os.Exit(1)
|
||||
|
||||
}
|
||||
|
||||
defer ipConn.Close()
|
||||
conn := tls.Client(ipConn, &tls.Config{
|
||||
InsecureSkipVerify: true,
|
||||
ServerName: u.Hostname(),
|
||||
})
|
||||
if err = conn.Handshake(); err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
defer conn.Close()
|
||||
addr := conn.RemoteAddr()
|
||||
_, _, err = net.SplitHostPort(addr.String())
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
cert := conn.ConnectionState().PeerCertificates[0]
|
||||
|
||||
timeNow := time.Now()
|
||||
if timeNow.After(cert.NotAfter) {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.String("issuer", cert.Issuer.CommonName),
|
||||
zap.String("subject", cert.Subject.CommonName),
|
||||
zap.Time("expired", cert.NotAfter))
|
||||
os.Exit(1)
|
||||
}
|
||||
|
||||
logger.Info("check succeed",
|
||||
zap.String("address", address),
|
||||
zap.String("issuer", cert.Issuer.CommonName),
|
||||
zap.String("subject", cert.Subject.CommonName),
|
||||
zap.Time("notAfter", cert.NotAfter),
|
||||
zap.Time("notBefore", cert.NotBefore))
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func fmtContentLength(b int64) string {
|
||||
const unit = 1000
|
||||
if b < unit {
|
||||
return fmt.Sprintf("%d B", b)
|
||||
}
|
||||
div, exp := int64(unit), 0
|
||||
for n := b / unit; n >= unit; n /= unit {
|
||||
div *= unit
|
||||
exp++
|
||||
}
|
||||
return fmt.Sprintf("%.1f %cB", float64(b)/float64(div), "kMGTPE"[exp])
|
||||
}
|
||||
|
||||
func runCheckWs(cmd *cobra.Command, args []string) error {
|
||||
if retryCount < 0 {
|
||||
return fmt.Errorf("--retry is required")
|
||||
}
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required! example: check ws wss://localhost:9898/ws/echo")
|
||||
}
|
||||
|
||||
address := args[0]
|
||||
if !strings.HasPrefix(address, "ws://") && !strings.HasPrefix(address, "wss://") {
|
||||
return fmt.Errorf("address must start with ws:// or wss://")
|
||||
}
|
||||
|
||||
for n := 0; n <= retryCount; n++ {
|
||||
if n != 0 {
|
||||
time.Sleep(retryDelay)
|
||||
}
|
||||
|
||||
dialer := websocket.Dialer{
|
||||
HandshakeTimeout: timeout,
|
||||
}
|
||||
|
||||
conn, _, err := dialer.Dial(address, nil)
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
|
||||
msg := "podinfo-check"
|
||||
start := time.Now()
|
||||
|
||||
conn.SetWriteDeadline(start.Add(timeout))
|
||||
if err := conn.WriteMessage(websocket.TextMessage, []byte(msg)); err != nil {
|
||||
conn.Close()
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
|
||||
conn.SetReadDeadline(time.Now().Add(timeout))
|
||||
_, resp, err := conn.ReadMessage()
|
||||
if err != nil {
|
||||
conn.Close()
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
|
||||
rtt := time.Since(start)
|
||||
conn.Close()
|
||||
|
||||
logger.Info("check succeed",
|
||||
zap.String("address", address),
|
||||
zap.Duration("round-trip", rtt),
|
||||
zap.Int("response size", len(resp)))
|
||||
os.Exit(0)
|
||||
}
|
||||
|
||||
os.Exit(1)
|
||||
return nil
|
||||
}
|
||||
|
||||
func runCheckgPRC(cmd *cobra.Command, args []string) error {
|
||||
if retryCount < 0 {
|
||||
return fmt.Errorf("--retry is required")
|
||||
}
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required! example: check grpc localhost:8080")
|
||||
}
|
||||
address := args[0]
|
||||
|
||||
var creds grpc.DialOption
|
||||
if grpcTLS {
|
||||
creds = grpc.WithTransportCredentials(credentials.NewTLS(&tls.Config{}))
|
||||
} else {
|
||||
creds = grpc.WithTransportCredentials(insecure.NewCredentials())
|
||||
}
|
||||
|
||||
for n := 0; n <= retryCount; n++ {
|
||||
if n != 0 {
|
||||
time.Sleep(retryDelay)
|
||||
}
|
||||
|
||||
conn, err := grpc.NewClient(address, creds)
|
||||
if err != nil {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
continue
|
||||
}
|
||||
ctx, cancel := context.WithTimeout(context.Background(), timeout)
|
||||
resp, err := grpc_health_v1.NewHealthClient(conn).Check(ctx, &grpc_health_v1.HealthCheckRequest{
|
||||
Service: grpcServiceName,
|
||||
})
|
||||
cancel()
|
||||
|
||||
if err != nil {
|
||||
if stat, ok := status.FromError(err); ok && stat.Code() == codes.Unimplemented {
|
||||
logger.Info("gRPC health protocol not implemented")
|
||||
os.Exit(1)
|
||||
} else {
|
||||
logger.Info("check failed",
|
||||
zap.String("address", address),
|
||||
zap.Error(err))
|
||||
}
|
||||
conn.Close()
|
||||
continue
|
||||
}
|
||||
|
||||
conn.Close()
|
||||
logger.Info("check succeed",
|
||||
zap.String("status", resp.GetStatus().String()))
|
||||
os.Exit(0)
|
||||
}
|
||||
|
||||
os.Exit(1)
|
||||
return nil
|
||||
}
|
||||
@@ -1,39 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"log"
|
||||
"os"
|
||||
"strings"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"go.uber.org/zap"
|
||||
)
|
||||
|
||||
var rootCmd = &cobra.Command{
|
||||
Use: "podcli",
|
||||
Short: "podinfo command line",
|
||||
Long: `
|
||||
podinfo command line utilities`,
|
||||
}
|
||||
|
||||
var (
|
||||
logger *zap.Logger
|
||||
)
|
||||
|
||||
func main() {
|
||||
|
||||
var err error
|
||||
logger, err = zap.NewDevelopment()
|
||||
if err != nil {
|
||||
log.Fatalf("can't initialize zap logger: %v", err)
|
||||
}
|
||||
defer logger.Sync()
|
||||
|
||||
rootCmd.SetArgs(os.Args[1:])
|
||||
if err := rootCmd.Execute(); err != nil {
|
||||
e := err.Error()
|
||||
fmt.Println(strings.ToUpper(e[:1]) + e[1:])
|
||||
os.Exit(1)
|
||||
}
|
||||
}
|
||||
@@ -1,21 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
|
||||
"github.com/spf13/cobra"
|
||||
"github.com/stefanprodan/podinfo/pkg/version"
|
||||
)
|
||||
|
||||
func init() {
|
||||
rootCmd.AddCommand(versionCmd)
|
||||
}
|
||||
|
||||
var versionCmd = &cobra.Command{
|
||||
Use: `version`,
|
||||
Short: "Prints podcli version",
|
||||
RunE: func(cmd *cobra.Command, args []string) error {
|
||||
fmt.Println(version.VERSION)
|
||||
return nil
|
||||
},
|
||||
}
|
||||
143
cmd/podcli/ws.go
143
cmd/podcli/ws.go
@@ -1,143 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"encoding/hex"
|
||||
"fmt"
|
||||
"net/http"
|
||||
"net/url"
|
||||
"os"
|
||||
"regexp"
|
||||
"strings"
|
||||
|
||||
"github.com/chzyer/readline"
|
||||
"github.com/fatih/color"
|
||||
"github.com/gorilla/websocket"
|
||||
"github.com/spf13/cobra"
|
||||
"go.uber.org/zap"
|
||||
)
|
||||
|
||||
var origin string
|
||||
|
||||
func init() {
|
||||
wsCmd.Flags().StringVarP(&origin, "origin", "o", "", "websocket origin")
|
||||
rootCmd.AddCommand(wsCmd)
|
||||
}
|
||||
|
||||
var wsCmd = &cobra.Command{
|
||||
Use: `ws [address]`,
|
||||
Short: "Websocket client",
|
||||
Example: ` ws localhost:9898/ws/echo`,
|
||||
RunE: func(cmd *cobra.Command, args []string) error {
|
||||
if len(args) < 1 {
|
||||
return fmt.Errorf("address is required")
|
||||
}
|
||||
|
||||
address := args[0]
|
||||
if !strings.HasPrefix(address, "ws://") && !strings.HasPrefix(address, "wss://") {
|
||||
address = fmt.Sprintf("ws://%s", address)
|
||||
}
|
||||
|
||||
dest, err := url.Parse(address)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
if origin != "" {
|
||||
} else {
|
||||
originURL := *dest
|
||||
if dest.Scheme == "wss" {
|
||||
originURL.Scheme = "https"
|
||||
} else {
|
||||
originURL.Scheme = "http"
|
||||
}
|
||||
origin = originURL.String()
|
||||
}
|
||||
|
||||
err = connect(dest.String(), origin, &readline.Config{
|
||||
Prompt: "> ",
|
||||
})
|
||||
if err != nil {
|
||||
logger.Info("websocket closed", zap.Error(err))
|
||||
}
|
||||
return nil
|
||||
},
|
||||
}
|
||||
|
||||
type session struct {
|
||||
ws *websocket.Conn
|
||||
rl *readline.Instance
|
||||
errChan chan error
|
||||
}
|
||||
|
||||
func connect(url, origin string, rlConf *readline.Config) error {
|
||||
headers := make(http.Header)
|
||||
headers.Add("Origin", origin)
|
||||
|
||||
ws, _, err := websocket.DefaultDialer.Dial(url, headers)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
rl, err := readline.NewEx(rlConf)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
defer rl.Close()
|
||||
|
||||
sess := &session{
|
||||
ws: ws,
|
||||
rl: rl,
|
||||
errChan: make(chan error),
|
||||
}
|
||||
|
||||
go sess.readConsole()
|
||||
go sess.readWebsocket()
|
||||
|
||||
return <-sess.errChan
|
||||
}
|
||||
|
||||
func (s *session) readConsole() {
|
||||
for {
|
||||
line, err := s.rl.Readline()
|
||||
if err != nil {
|
||||
s.errChan <- err
|
||||
return
|
||||
}
|
||||
|
||||
err = s.ws.WriteMessage(websocket.TextMessage, []byte(line))
|
||||
if err != nil {
|
||||
s.errChan <- err
|
||||
return
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
func bytesToFormattedHex(bytes []byte) string {
|
||||
text := hex.EncodeToString(bytes)
|
||||
return regexp.MustCompile("(..)").ReplaceAllString(text, "$1 ")
|
||||
}
|
||||
|
||||
func (s *session) readWebsocket() {
|
||||
rxSprintf := color.New(color.FgGreen).SprintfFunc()
|
||||
|
||||
for {
|
||||
msgType, buf, err := s.ws.ReadMessage()
|
||||
if err != nil {
|
||||
fmt.Fprint(s.rl.Stdout(), rxSprintf("< %s\n", err.Error()))
|
||||
os.Exit(1)
|
||||
return
|
||||
}
|
||||
|
||||
var text string
|
||||
switch msgType {
|
||||
case websocket.TextMessage:
|
||||
text = string(buf)
|
||||
case websocket.BinaryMessage:
|
||||
text = bytesToFormattedHex(buf)
|
||||
default:
|
||||
s.errChan <- fmt.Errorf("unknown websocket frame type: %d", msgType)
|
||||
return
|
||||
}
|
||||
|
||||
fmt.Fprint(s.rl.Stdout(), rxSprintf("< %s\n", text))
|
||||
}
|
||||
}
|
||||
@@ -1,256 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"os"
|
||||
"path/filepath"
|
||||
"strconv"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/spf13/pflag"
|
||||
"github.com/spf13/viper"
|
||||
"go.uber.org/zap"
|
||||
"go.uber.org/zap/zapcore"
|
||||
|
||||
"github.com/stefanprodan/podinfo/pkg/api/grpc"
|
||||
"github.com/stefanprodan/podinfo/pkg/api/http"
|
||||
"github.com/stefanprodan/podinfo/pkg/signals"
|
||||
"github.com/stefanprodan/podinfo/pkg/version"
|
||||
go_grpc "google.golang.org/grpc"
|
||||
)
|
||||
|
||||
func main() {
|
||||
// flags definition
|
||||
fs := pflag.NewFlagSet("default", pflag.ContinueOnError)
|
||||
fs.String("host", "", "Host to bind service to")
|
||||
fs.Int("port", 9898, "HTTP port to bind service to")
|
||||
fs.Int("secure-port", 0, "HTTPS port")
|
||||
fs.Int("port-metrics", 0, "metrics port")
|
||||
fs.Int("grpc-port", 0, "gRPC port")
|
||||
fs.String("grpc-service-name", "podinfo", "gPRC service name")
|
||||
fs.String("level", "info", "log level debug, info, warn, error, fatal or panic")
|
||||
fs.StringSlice("backend-url", []string{}, "backend service URL")
|
||||
fs.Duration("http-client-timeout", 2*time.Minute, "client timeout duration")
|
||||
fs.Duration("http-server-timeout", 30*time.Second, "server read and write timeout duration")
|
||||
fs.Duration("server-shutdown-timeout", 5*time.Second, "server graceful shutdown timeout duration")
|
||||
fs.String("data-path", "/data", "data local path")
|
||||
fs.String("config-path", "", "config dir path")
|
||||
fs.String("cert-path", "/data/cert", "certificate path for HTTPS port")
|
||||
fs.String("config", "config.yaml", "config file name")
|
||||
fs.String("ui-path", "./ui", "UI local path")
|
||||
fs.String("ui-logo", "", "UI logo")
|
||||
fs.String("ui-color", "#34577c", "UI color")
|
||||
fs.String("ui-message", fmt.Sprintf("greetings from podinfo v%v", version.VERSION), "UI message")
|
||||
fs.Bool("h2c", false, "allow upgrading to H2C")
|
||||
fs.Bool("random-delay", false, "between 0 and 5 seconds random delay by default")
|
||||
fs.String("random-delay-unit", "s", "either s(seconds) or ms(milliseconds")
|
||||
fs.Int("random-delay-min", 0, "min for random delay: 0 by default")
|
||||
fs.Int("random-delay-max", 5, "max for random delay: 5 by default")
|
||||
fs.Bool("random-error", false, "1/3 chances of a random response error")
|
||||
fs.Bool("unhealthy", false, "when set, healthy state is never reached")
|
||||
fs.Bool("unready", false, "when set, ready state is never reached")
|
||||
fs.Int("stress-cpu", 0, "number of CPU cores with 100 load")
|
||||
fs.Int("stress-memory", 0, "MB of data to load into memory")
|
||||
fs.String("cache-server", "", "Redis address in the format 'tcp://<host>:<port>'")
|
||||
fs.String("otel-service-name", "", "service name for reporting to open telemetry address, when not set tracing is disabled")
|
||||
|
||||
versionFlag := fs.BoolP("version", "v", false, "get version number")
|
||||
|
||||
// parse flags
|
||||
err := fs.Parse(os.Args[1:])
|
||||
switch {
|
||||
case err == pflag.ErrHelp:
|
||||
os.Exit(0)
|
||||
case err != nil:
|
||||
fmt.Fprintf(os.Stderr, "Error: %s\n\n", err.Error())
|
||||
fs.PrintDefaults()
|
||||
os.Exit(2)
|
||||
case *versionFlag:
|
||||
fmt.Println(version.VERSION)
|
||||
os.Exit(0)
|
||||
}
|
||||
|
||||
// bind flags and environment variables
|
||||
viper.BindPFlags(fs)
|
||||
viper.RegisterAlias("backendUrl", "backend-url")
|
||||
hostname, _ := os.Hostname()
|
||||
viper.SetDefault("jwt-secret", "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9")
|
||||
viper.SetDefault("ui-logo", "https://raw.githubusercontent.com/stefanprodan/podinfo/gh-pages/cuddle_clap.gif")
|
||||
viper.Set("hostname", hostname)
|
||||
viper.Set("version", version.VERSION)
|
||||
viper.Set("revision", version.REVISION)
|
||||
viper.SetEnvPrefix("PODINFO")
|
||||
viper.SetEnvKeyReplacer(strings.NewReplacer("-", "_"))
|
||||
viper.AutomaticEnv()
|
||||
|
||||
// load config from file
|
||||
if _, fileErr := os.Stat(filepath.Join(viper.GetString("config-path"), viper.GetString("config"))); fileErr == nil {
|
||||
viper.SetConfigName(strings.Split(viper.GetString("config"), ".")[0])
|
||||
viper.AddConfigPath(viper.GetString("config-path"))
|
||||
if readErr := viper.ReadInConfig(); readErr != nil {
|
||||
fmt.Printf("Error reading config file, %v\n", readErr)
|
||||
}
|
||||
}
|
||||
|
||||
// configure logging
|
||||
logger, _ := initZap(viper.GetString("level"))
|
||||
defer logger.Sync()
|
||||
stdLog := zap.RedirectStdLog(logger)
|
||||
defer stdLog()
|
||||
|
||||
// start stress tests if any
|
||||
beginStressTest(viper.GetInt("stress-cpu"), viper.GetInt("stress-memory"), logger)
|
||||
|
||||
// validate port
|
||||
if _, err := strconv.Atoi(viper.GetString("port")); err != nil {
|
||||
port, _ := fs.GetInt("port")
|
||||
viper.Set("port", strconv.Itoa(port))
|
||||
}
|
||||
|
||||
// validate secure port
|
||||
if _, err := strconv.Atoi(viper.GetString("secure-port")); err != nil {
|
||||
securePort, _ := fs.GetInt("secure-port")
|
||||
viper.Set("secure-port", strconv.Itoa(securePort))
|
||||
}
|
||||
|
||||
// validate random delay options
|
||||
if viper.GetInt("random-delay-max") < viper.GetInt("random-delay-min") {
|
||||
logger.Panic("`--random-delay-max` should be greater than `--random-delay-min`")
|
||||
}
|
||||
|
||||
switch delayUnit := viper.GetString("random-delay-unit"); delayUnit {
|
||||
case
|
||||
"s",
|
||||
"ms":
|
||||
break
|
||||
default:
|
||||
logger.Panic("`random-delay-unit` accepted values are: s|ms")
|
||||
}
|
||||
|
||||
// load gRPC server config
|
||||
var grpcCfg grpc.Config
|
||||
if err := viper.Unmarshal(&grpcCfg); err != nil {
|
||||
logger.Panic("config unmarshal failed", zap.Error(err))
|
||||
}
|
||||
|
||||
// start gRPC server
|
||||
var grpcServer *go_grpc.Server
|
||||
if grpcCfg.Port > 0 {
|
||||
grpcSrv, _ := grpc.NewServer(&grpcCfg, logger)
|
||||
//grpcinfoSrv, _ := grpc.NewInfoServer(&grpcCfg)
|
||||
|
||||
grpcServer = grpcSrv.ListenAndServe()
|
||||
}
|
||||
|
||||
// load HTTP server config
|
||||
var srvCfg http.Config
|
||||
if err := viper.Unmarshal(&srvCfg); err != nil {
|
||||
logger.Panic("config unmarshal failed", zap.Error(err))
|
||||
}
|
||||
|
||||
// log version and port
|
||||
logger.Info("Starting podinfo",
|
||||
zap.String("version", viper.GetString("version")),
|
||||
zap.String("revision", viper.GetString("revision")),
|
||||
zap.String("port", srvCfg.Port),
|
||||
)
|
||||
|
||||
// start HTTP server
|
||||
srv, _ := http.NewServer(&srvCfg, logger)
|
||||
httpServer, httpsServer, healthy, ready := srv.ListenAndServe()
|
||||
|
||||
// graceful shutdown
|
||||
stopCh := signals.SetupSignalHandler()
|
||||
sd, _ := signals.NewShutdown(srvCfg.ServerShutdownTimeout, logger)
|
||||
sd.Graceful(stopCh, httpServer, httpsServer, grpcServer, healthy, ready)
|
||||
}
|
||||
|
||||
func initZap(logLevel string) (*zap.Logger, error) {
|
||||
level := zap.NewAtomicLevelAt(zapcore.InfoLevel)
|
||||
switch logLevel {
|
||||
case "debug":
|
||||
level = zap.NewAtomicLevelAt(zapcore.DebugLevel)
|
||||
case "info":
|
||||
level = zap.NewAtomicLevelAt(zapcore.InfoLevel)
|
||||
case "warn":
|
||||
level = zap.NewAtomicLevelAt(zapcore.WarnLevel)
|
||||
case "error":
|
||||
level = zap.NewAtomicLevelAt(zapcore.ErrorLevel)
|
||||
case "fatal":
|
||||
level = zap.NewAtomicLevelAt(zapcore.FatalLevel)
|
||||
case "panic":
|
||||
level = zap.NewAtomicLevelAt(zapcore.PanicLevel)
|
||||
}
|
||||
|
||||
zapEncoderConfig := zapcore.EncoderConfig{
|
||||
TimeKey: "ts",
|
||||
LevelKey: "level",
|
||||
NameKey: "logger",
|
||||
CallerKey: "caller",
|
||||
MessageKey: "msg",
|
||||
StacktraceKey: "stacktrace",
|
||||
LineEnding: zapcore.DefaultLineEnding,
|
||||
EncodeLevel: zapcore.LowercaseLevelEncoder,
|
||||
EncodeTime: zapcore.ISO8601TimeEncoder,
|
||||
EncodeDuration: zapcore.SecondsDurationEncoder,
|
||||
EncodeCaller: zapcore.ShortCallerEncoder,
|
||||
}
|
||||
|
||||
zapConfig := zap.Config{
|
||||
Level: level,
|
||||
Development: false,
|
||||
Sampling: &zap.SamplingConfig{
|
||||
Initial: 100,
|
||||
Thereafter: 100,
|
||||
},
|
||||
Encoding: "json",
|
||||
EncoderConfig: zapEncoderConfig,
|
||||
OutputPaths: []string{"stderr"},
|
||||
ErrorOutputPaths: []string{"stderr"},
|
||||
}
|
||||
|
||||
return zapConfig.Build()
|
||||
}
|
||||
|
||||
var stressMemoryPayload []byte
|
||||
|
||||
func beginStressTest(cpus int, mem int, logger *zap.Logger) {
|
||||
done := make(chan int)
|
||||
if cpus > 0 {
|
||||
logger.Info("starting CPU stress", zap.Int("cores", cpus))
|
||||
for i := 0; i < cpus; i++ {
|
||||
go func() {
|
||||
for {
|
||||
select {
|
||||
case <-done:
|
||||
return
|
||||
default:
|
||||
|
||||
}
|
||||
}
|
||||
}()
|
||||
}
|
||||
}
|
||||
|
||||
if mem > 0 {
|
||||
path := "/tmp/podinfo.data"
|
||||
f, err := os.Create(path)
|
||||
|
||||
if err != nil {
|
||||
logger.Error("memory stress failed", zap.Error(err))
|
||||
}
|
||||
|
||||
if err := f.Truncate(1000000 * int64(mem)); err != nil {
|
||||
logger.Error("memory stress failed", zap.Error(err))
|
||||
}
|
||||
|
||||
stressMemoryPayload, err = os.ReadFile(path)
|
||||
f.Close()
|
||||
os.Remove(path)
|
||||
if err != nil {
|
||||
logger.Error("memory stress failed", zap.Error(err))
|
||||
}
|
||||
logger.Info("starting MEMORY stress", zap.Int("memory", len(stressMemoryPayload)))
|
||||
}
|
||||
}
|
||||
BIN
cuddle_bunny.gif
Normal file
BIN
cuddle_bunny.gif
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 50 KiB |
BIN
cuddle_clap.gif
Normal file
BIN
cuddle_clap.gif
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 42 KiB |
@@ -1,45 +0,0 @@
|
||||
# Deploy demo webapp
|
||||
|
||||
Demo webapp manifests:
|
||||
|
||||
- [common](webapp/common)
|
||||
- [frontend](webapp/frontend)
|
||||
- [backend](webapp/backend)
|
||||
|
||||
Deploy the demo in `webapp` namespace:
|
||||
|
||||
```bash
|
||||
kubectl apply -f ./webapp/common
|
||||
kubectl apply -f ./webapp/backend
|
||||
kubectl apply -f ./webapp/frontend
|
||||
```
|
||||
|
||||
Deploy the demo in the `dev` namespace:
|
||||
|
||||
```bash
|
||||
kustomize build ./overlays/dev | kubectl apply -f-
|
||||
```
|
||||
|
||||
Deploy the demo in the `staging` namespace:
|
||||
|
||||
```bash
|
||||
kustomize build ./overlays/staging | kubectl apply -f-
|
||||
```
|
||||
|
||||
Deploy the demo in the `production` namespace:
|
||||
|
||||
```bash
|
||||
kustomize build ./overlays/production | kubectl apply -f-
|
||||
```
|
||||
|
||||
## Testing Locally Using Kind
|
||||
|
||||
> NOTE: You can install [kind from here](https://kind.sigs.k8s.io/docs/user/quick-start/#installation)
|
||||
|
||||
The following will create a new cluster called "podinfo" and configure host ports on 80 and 443. You can access the
|
||||
endpoints on localhost. The example also deploys cert-manager within the cluster along with a self-signed cluster issuer
|
||||
used to generate the certificate to validate the secure port.
|
||||
|
||||
```sh
|
||||
./kind.sh
|
||||
```
|
||||
@@ -1,73 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: backend
|
||||
spec:
|
||||
minReadySeconds: 3
|
||||
revisionHistoryLimit: 5
|
||||
progressDeadlineSeconds: 60
|
||||
strategy:
|
||||
rollingUpdate:
|
||||
maxUnavailable: 0
|
||||
type: RollingUpdate
|
||||
selector:
|
||||
matchLabels:
|
||||
app.kubernetes.io/name: backend
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "9797"
|
||||
labels:
|
||||
app.kubernetes.io/name: backend
|
||||
spec:
|
||||
containers:
|
||||
- name: backend
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
ports:
|
||||
- name: http
|
||||
containerPort: 9898
|
||||
protocol: TCP
|
||||
- name: http-metrics
|
||||
containerPort: 9797
|
||||
protocol: TCP
|
||||
- name: grpc
|
||||
containerPort: 9999
|
||||
protocol: TCP
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port=9898
|
||||
- --port-metrics=9797
|
||||
- --grpc-port=9999
|
||||
- --grpc-service-name=backend
|
||||
- --level=info
|
||||
- --cache-server=tcp://cache:6379
|
||||
env:
|
||||
- name: PODINFO_UI_COLOR
|
||||
value: "#34577c"
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/healthz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/readyz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 512Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
@@ -1,18 +0,0 @@
|
||||
apiVersion: autoscaling/v2
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
name: backend
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: backend
|
||||
minReplicas: 1
|
||||
maxReplicas: 2
|
||||
metrics:
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: 99
|
||||
@@ -1,7 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
resources:
|
||||
- service.yaml
|
||||
- deployment.yaml
|
||||
- hpa.yaml
|
||||
|
||||
@@ -1,17 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: backend
|
||||
spec:
|
||||
type: ClusterIP
|
||||
selector:
|
||||
app.kubernetes.io/name: backend
|
||||
ports:
|
||||
- name: http
|
||||
port: 9898
|
||||
protocol: TCP
|
||||
targetPort: http
|
||||
- port: 9999
|
||||
targetPort: grpc
|
||||
protocol: TCP
|
||||
name: grpc
|
||||
57
deploy/bases/cache/deployment.yaml
vendored
57
deploy/bases/cache/deployment.yaml
vendored
@@ -1,57 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: cache
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
app.kubernetes.io/name: cache
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app.kubernetes.io/name: cache
|
||||
spec:
|
||||
containers:
|
||||
- name: redis
|
||||
image: docker.io/redis:8.6.1
|
||||
imagePullPolicy: IfNotPresent
|
||||
command:
|
||||
- redis-server
|
||||
- "/redis-master/redis.conf"
|
||||
ports:
|
||||
- name: redis
|
||||
containerPort: 6379
|
||||
protocol: TCP
|
||||
livenessProbe:
|
||||
tcpSocket:
|
||||
port: redis
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- redis-cli
|
||||
- ping
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 128Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
volumeMounts:
|
||||
- mountPath: /var/lib/redis
|
||||
name: data
|
||||
- mountPath: /redis-master
|
||||
name: config
|
||||
volumes:
|
||||
- name: data
|
||||
emptyDir: {}
|
||||
- name: config
|
||||
configMap:
|
||||
name: redis-config
|
||||
items:
|
||||
- key: redis.conf
|
||||
path: redis.conf
|
||||
9
deploy/bases/cache/kustomization.yaml
vendored
9
deploy/bases/cache/kustomization.yaml
vendored
@@ -1,9 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
resources:
|
||||
- service.yaml
|
||||
- deployment.yaml
|
||||
configMapGenerator:
|
||||
- name: redis-config
|
||||
files:
|
||||
- redis.conf
|
||||
4
deploy/bases/cache/redis.conf
vendored
4
deploy/bases/cache/redis.conf
vendored
@@ -1,4 +0,0 @@
|
||||
maxmemory 64mb
|
||||
maxmemory-policy allkeys-lru
|
||||
save ""
|
||||
appendonly no
|
||||
13
deploy/bases/cache/service.yaml
vendored
13
deploy/bases/cache/service.yaml
vendored
@@ -1,13 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: cache
|
||||
spec:
|
||||
type: ClusterIP
|
||||
selector:
|
||||
app.kubernetes.io/name: cache
|
||||
ports:
|
||||
- name: redis
|
||||
port: 6379
|
||||
protocol: TCP
|
||||
targetPort: redis
|
||||
@@ -1,76 +0,0 @@
|
||||
# Database Setup
|
||||
|
||||
This directory contains the Kubernetes manifests to simulate a database setup
|
||||
with a primary database, read replicas, and scheduled maintenance tasks using CronJobs.
|
||||
|
||||
## Components
|
||||
|
||||
### Core Resources
|
||||
|
||||
| Resource | File | Description |
|
||||
|----------|------|-------------|
|
||||
| ServiceAccount | `serviceaccount.yaml` | Shared service account for all database workloads |
|
||||
| PVC | `pvc-primary.yaml` | 1Gi persistent storage for primary database |
|
||||
| StatefulSet | `statefulset-primary.yaml` | Primary database with persistent storage at `/data` |
|
||||
| Deployment | `deployment-replica.yaml` | Read replica deployment |
|
||||
| Service (Headless) | `service-primary.yaml` | Headless service for StatefulSet |
|
||||
| Service | `service-replica.yaml` | ClusterIP service for replicas |
|
||||
| HPA | `hpa-replica.yaml` | Autoscaler for replicas (2-3 pods, 99% CPU) |
|
||||
|
||||
### CronJobs
|
||||
|
||||
| CronJob | Schedule | Duration | TTL Cleanup | Description |
|
||||
|---------|----------|----------|-------------|-------------|
|
||||
| `rollup-daily` | Every 10 min | ~1 min | 1 hour | Daily rollup simulation (6 iterations) |
|
||||
| `rollup-weekly` | Every 30 min | ~2 min | 1 day | Weekly rollup simulation (12 iterations) |
|
||||
| `backup-daily` | Daily at midnight | ~1 min | 1 day | Backup simulation (configured to fail) |
|
||||
|
||||
### Scripts
|
||||
|
||||
Located in `scripts/` directory:
|
||||
|
||||
- `rollup.sh` - Rollup simulation script with configurable steps via `ROLLUP_STEPS` env var
|
||||
- `backup.sh` - Backup simulation script with configurable exit code via `BACKUP_EXIT` env var
|
||||
|
||||
## Labels
|
||||
|
||||
All resources use Kubernetes recommended labels:
|
||||
|
||||
- `app.kubernetes.io/name` - Component name
|
||||
- `app.kubernetes.io/part-of: database` - Part of database application
|
||||
|
||||
## Configuration
|
||||
|
||||
### Primary Database
|
||||
- **Port**: 3306 (MySQL standard)
|
||||
- **Storage**: 1Gi PersistentVolumeClaim mounted at `/data`
|
||||
- **Service**: Headless (`clusterIP: None`) for StatefulSet
|
||||
|
||||
### Replica Database
|
||||
- **Port**: 3306
|
||||
- **Scaling**: HPA with 2-3 replicas at 99% CPU utilization
|
||||
- **Service**: ClusterIP
|
||||
|
||||
### CronJob Scripts
|
||||
|
||||
The scripts check database-replica health before running:
|
||||
|
||||
```sh
|
||||
podcli check http database-replica:3306/readyz
|
||||
```
|
||||
|
||||
## Usage
|
||||
|
||||
Deploy with Kustomize:
|
||||
|
||||
```bash
|
||||
kubectl apply -k deploy/bases/database
|
||||
```
|
||||
|
||||
Or include in an overlay:
|
||||
|
||||
```yaml
|
||||
# kustomization.yaml
|
||||
resources:
|
||||
- ../../bases/database
|
||||
```
|
||||
@@ -1,48 +0,0 @@
|
||||
apiVersion: batch/v1
|
||||
kind: CronJob
|
||||
metadata:
|
||||
name: backup-daily
|
||||
spec:
|
||||
# Runs every day at midnight for 1 minute
|
||||
schedule: "0 0 * * *"
|
||||
concurrencyPolicy: Forbid
|
||||
successfulJobsHistoryLimit: 1
|
||||
failedJobsHistoryLimit: 1
|
||||
jobTemplate:
|
||||
spec:
|
||||
# Cleanup after 1 day
|
||||
ttlSecondsAfterFinished: 86400
|
||||
backoffLimit: 1
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app.kubernetes.io/name: backup-daily
|
||||
app.kubernetes.io/part-of: database
|
||||
spec:
|
||||
serviceAccountName: database
|
||||
restartPolicy: Never
|
||||
containers:
|
||||
- name: backup
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
command:
|
||||
- /bin/sh
|
||||
- /scripts/backup.sh
|
||||
env:
|
||||
- name: BACKUP_EXIT
|
||||
value: "1"
|
||||
resources:
|
||||
limits:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
requests:
|
||||
cpu: 10m
|
||||
memory: 16Mi
|
||||
volumeMounts:
|
||||
- name: scripts
|
||||
mountPath: /scripts
|
||||
volumes:
|
||||
- name: scripts
|
||||
configMap:
|
||||
name: backup-script
|
||||
defaultMode: 0755
|
||||
@@ -1,48 +0,0 @@
|
||||
apiVersion: batch/v1
|
||||
kind: CronJob
|
||||
metadata:
|
||||
name: rollup-daily
|
||||
spec:
|
||||
# Runs every 10 minutes for 1 minute
|
||||
schedule: "*/10 * * * *"
|
||||
concurrencyPolicy: Forbid
|
||||
successfulJobsHistoryLimit: 1
|
||||
failedJobsHistoryLimit: 1
|
||||
jobTemplate:
|
||||
spec:
|
||||
# Cleanup after 1 hour
|
||||
ttlSecondsAfterFinished: 3600
|
||||
backoffLimit: 3
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app.kubernetes.io/name: rollup-daily
|
||||
app.kubernetes.io/part-of: database
|
||||
spec:
|
||||
serviceAccountName: database
|
||||
restartPolicy: OnFailure
|
||||
containers:
|
||||
- name: healthcheck
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
command:
|
||||
- /bin/sh
|
||||
- /scripts/rollup.sh
|
||||
env:
|
||||
- name: ROLLUP_STEPS
|
||||
value: "6"
|
||||
resources:
|
||||
limits:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
requests:
|
||||
cpu: 10m
|
||||
memory: 16Mi
|
||||
volumeMounts:
|
||||
- name: scripts
|
||||
mountPath: /scripts
|
||||
volumes:
|
||||
- name: scripts
|
||||
configMap:
|
||||
name: rollup-script
|
||||
defaultMode: 0755
|
||||
@@ -1,48 +0,0 @@
|
||||
apiVersion: batch/v1
|
||||
kind: CronJob
|
||||
metadata:
|
||||
name: rollup-weekly
|
||||
spec:
|
||||
# Runs every 30 minutes for 2 minutes
|
||||
schedule: "*/30 * * * *"
|
||||
concurrencyPolicy: Forbid
|
||||
successfulJobsHistoryLimit: 1
|
||||
failedJobsHistoryLimit: 1
|
||||
jobTemplate:
|
||||
spec:
|
||||
# Cleanup after 1 day
|
||||
ttlSecondsAfterFinished: 86400
|
||||
backoffLimit: 3
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app.kubernetes.io/name: rollup-weekly
|
||||
app.kubernetes.io/part-of: database
|
||||
spec:
|
||||
serviceAccountName: database
|
||||
restartPolicy: OnFailure
|
||||
containers:
|
||||
- name: healthcheck
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
command:
|
||||
- /bin/sh
|
||||
- /scripts/rollup.sh
|
||||
env:
|
||||
- name: ROLLUP_STEPS
|
||||
value: "12"
|
||||
resources:
|
||||
limits:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
requests:
|
||||
cpu: 10m
|
||||
memory: 16Mi
|
||||
volumeMounts:
|
||||
- name: scripts
|
||||
mountPath: /scripts
|
||||
volumes:
|
||||
- name: scripts
|
||||
configMap:
|
||||
name: rollup-script
|
||||
defaultMode: 0755
|
||||
@@ -1,66 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: database-replica
|
||||
spec:
|
||||
minReadySeconds: 3
|
||||
revisionHistoryLimit: 5
|
||||
progressDeadlineSeconds: 60
|
||||
strategy:
|
||||
rollingUpdate:
|
||||
maxUnavailable: 0
|
||||
type: RollingUpdate
|
||||
selector:
|
||||
matchLabels:
|
||||
app.kubernetes.io/name: database-replica
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "9797"
|
||||
labels:
|
||||
app.kubernetes.io/name: database-replica
|
||||
app.kubernetes.io/part-of: database
|
||||
spec:
|
||||
serviceAccountName: database
|
||||
containers:
|
||||
- name: database
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
ports:
|
||||
- name: db
|
||||
containerPort: 3306
|
||||
protocol: TCP
|
||||
- name: http-metrics
|
||||
containerPort: 9797
|
||||
protocol: TCP
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port=3306
|
||||
- --port-metrics=9797
|
||||
- --level=info
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:3306/healthz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:3306/readyz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 512Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
@@ -1,18 +0,0 @@
|
||||
apiVersion: autoscaling/v2
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
name: database-replica
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: database-replica
|
||||
minReplicas: 2
|
||||
maxReplicas: 3
|
||||
metrics:
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: 99
|
||||
@@ -1,24 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
resources:
|
||||
- serviceaccount.yaml
|
||||
- pvc-primary.yaml
|
||||
- statefulset-primary.yaml
|
||||
- deployment-replica.yaml
|
||||
- service-primary.yaml
|
||||
- service-replica.yaml
|
||||
- hpa-replica.yaml
|
||||
- cronjob-rollup-daily.yaml
|
||||
- cronjob-rollup-weekly.yaml
|
||||
- cronjob-backup-daily.yaml
|
||||
configMapGenerator:
|
||||
- name: rollup-script
|
||||
files:
|
||||
- scripts/rollup.sh
|
||||
options:
|
||||
disableNameSuffixHash: true
|
||||
- name: backup-script
|
||||
files:
|
||||
- scripts/backup.sh
|
||||
options:
|
||||
disableNameSuffixHash: true
|
||||
@@ -1,10 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: PersistentVolumeClaim
|
||||
metadata:
|
||||
name: database-primary
|
||||
spec:
|
||||
accessModes:
|
||||
- ReadWriteOnce
|
||||
resources:
|
||||
requests:
|
||||
storage: 1Gi
|
||||
@@ -1,12 +0,0 @@
|
||||
#!/bin/sh
|
||||
set -e
|
||||
|
||||
# This is a simulation of a backup process.
|
||||
|
||||
EXIT_CODE=${BACKUP_EXIT:-0}
|
||||
|
||||
echo "Starting backup (estimated run time: 60s)"
|
||||
podcli check http database-replica:3306/readyz
|
||||
sleep 60
|
||||
echo "Backup finished"
|
||||
exit $EXIT_CODE
|
||||
@@ -1,15 +0,0 @@
|
||||
#!/bin/sh
|
||||
set -e
|
||||
|
||||
# This is a simulation of a rollup process.
|
||||
|
||||
STEPS=${ROLLUP_STEPS:-6}
|
||||
echo "Starting rollup with $STEPS steps (estimated run time: $((STEPS * 10))s)"
|
||||
podcli check http database-replica:3306/readyz
|
||||
i=1
|
||||
while [ $i -le $STEPS ]; do
|
||||
echo "Running rollup iteration $i of $STEPS"
|
||||
sleep 10
|
||||
i=$((i + 1))
|
||||
done
|
||||
echo "Rollup finished"
|
||||
@@ -1,14 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: database-primary
|
||||
spec:
|
||||
type: ClusterIP
|
||||
clusterIP: None
|
||||
selector:
|
||||
app.kubernetes.io/name: database-primary
|
||||
ports:
|
||||
- name: db
|
||||
port: 3306
|
||||
protocol: TCP
|
||||
targetPort: db
|
||||
@@ -1,13 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: database-replica
|
||||
spec:
|
||||
type: ClusterIP
|
||||
selector:
|
||||
app.kubernetes.io/name: database-replica
|
||||
ports:
|
||||
- name: db
|
||||
port: 3306
|
||||
protocol: TCP
|
||||
targetPort: db
|
||||
@@ -1,4 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: database
|
||||
@@ -1,70 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: StatefulSet
|
||||
metadata:
|
||||
name: database-primary
|
||||
spec:
|
||||
serviceName: database-primary
|
||||
replicas: 1
|
||||
minReadySeconds: 3
|
||||
revisionHistoryLimit: 5
|
||||
selector:
|
||||
matchLabels:
|
||||
app.kubernetes.io/name: database-primary
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "9797"
|
||||
labels:
|
||||
app.kubernetes.io/name: database-primary
|
||||
app.kubernetes.io/part-of: database
|
||||
spec:
|
||||
serviceAccountName: database
|
||||
containers:
|
||||
- name: database
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
ports:
|
||||
- name: db
|
||||
containerPort: 3306
|
||||
protocol: TCP
|
||||
- name: http-metrics
|
||||
containerPort: 9797
|
||||
protocol: TCP
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port=3306
|
||||
- --port-metrics=9797
|
||||
- --level=info
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:3306/healthz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:3306/readyz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 512Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
volumeMounts:
|
||||
- name: data
|
||||
mountPath: /data
|
||||
volumes:
|
||||
- name: data
|
||||
persistentVolumeClaim:
|
||||
claimName: database-primary
|
||||
@@ -1,72 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: frontend
|
||||
spec:
|
||||
minReadySeconds: 3
|
||||
revisionHistoryLimit: 5
|
||||
progressDeadlineSeconds: 60
|
||||
strategy:
|
||||
rollingUpdate:
|
||||
maxUnavailable: 0
|
||||
type: RollingUpdate
|
||||
selector:
|
||||
matchLabels:
|
||||
app.kubernetes.io/name: frontend
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "9797"
|
||||
labels:
|
||||
app.kubernetes.io/name: frontend
|
||||
spec:
|
||||
containers:
|
||||
- name: frontend
|
||||
image: ghcr.io/stefanprodan/podinfo:6.11.0
|
||||
imagePullPolicy: IfNotPresent
|
||||
ports:
|
||||
- name: http
|
||||
containerPort: 9898
|
||||
protocol: TCP
|
||||
- name: http-metrics
|
||||
containerPort: 9797
|
||||
protocol: TCP
|
||||
- name: grpc
|
||||
containerPort: 9999
|
||||
protocol: TCP
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port=9898
|
||||
- --port-metrics=9797
|
||||
- --level=info
|
||||
- --backend-url=http://backend:9898/echo
|
||||
- --cache-server=tcp://cache:6379
|
||||
env:
|
||||
- name: PODINFO_UI_COLOR
|
||||
value: "#34577c"
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/healthz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/readyz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 128Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
@@ -1,18 +0,0 @@
|
||||
apiVersion: autoscaling/v2
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
name: frontend
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: frontend
|
||||
minReplicas: 1
|
||||
maxReplicas: 4
|
||||
metrics:
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: 99
|
||||
@@ -1,7 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
resources:
|
||||
- service.yaml
|
||||
- deployment.yaml
|
||||
- hpa.yaml
|
||||
|
||||
@@ -1,13 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: frontend
|
||||
spec:
|
||||
type: ClusterIP
|
||||
selector:
|
||||
app.kubernetes.io/name: frontend
|
||||
ports:
|
||||
- name: http
|
||||
port: 80
|
||||
protocol: TCP
|
||||
targetPort: http
|
||||
@@ -1,48 +0,0 @@
|
||||
#! /usr/bin/env sh
|
||||
|
||||
mkdir -p bin
|
||||
cat > ./bin/kind.yaml <<EOF
|
||||
apiVersion: kind.x-k8s.io/v1alpha4
|
||||
kind: Cluster
|
||||
nodes:
|
||||
- role: control-plane
|
||||
extraPortMappings:
|
||||
- containerPort: 80
|
||||
hostPort: 80
|
||||
protocol: TCP
|
||||
- containerPort: 443
|
||||
hostPort: 443
|
||||
protocol: TCP
|
||||
EOF
|
||||
|
||||
# create the kind cluster
|
||||
kind create cluster --config=kind.yaml
|
||||
|
||||
# add certificate manager
|
||||
kubectl apply -f https://github.com/jetstack/cert-manager/releases/download/v1.0.4/cert-manager.yaml
|
||||
|
||||
# wait for cert manager
|
||||
kubectl rollout status --namespace cert-manager deployment/cert-manager --timeout=2m
|
||||
kubectl rollout status --namespace cert-manager deployment/cert-manager-webhook --timeout=2m
|
||||
kubectl rollout status --namespace cert-manager deployment/cert-manager-cainjector --timeout=2m
|
||||
|
||||
# # apply the secure webapp
|
||||
kubectl apply -f ./secure/common
|
||||
kubectl apply -f ./secure/backend
|
||||
kubectl apply -f ./secure/frontend
|
||||
|
||||
# # wait for the podinfo frontend to come up
|
||||
kubectl rollout status --namespace secure deployment/frontend --timeout=1m
|
||||
|
||||
# curl the endpoints (responds with info due to header regexp on route handler)
|
||||
echo
|
||||
echo "http enpdoint:"
|
||||
echo "curl http://localhost"
|
||||
echo
|
||||
curl http://localhost
|
||||
|
||||
echo
|
||||
echo "https (secure) enpdoint:"
|
||||
echo "curl --insecure https://localhost"
|
||||
echo
|
||||
curl --insecure https://localhost
|
||||
@@ -1,11 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
namespace: dev
|
||||
resources:
|
||||
- ../../bases/backend
|
||||
- ../../bases/frontend
|
||||
- ../../bases/cache
|
||||
- ../../bases/database
|
||||
- namespace.yaml
|
||||
transformers:
|
||||
- labels.yaml
|
||||
@@ -1,10 +0,0 @@
|
||||
apiVersion: builtin
|
||||
kind: LabelTransformer
|
||||
metadata:
|
||||
name: labels
|
||||
labels:
|
||||
app.kubernetes.io/environment: dev
|
||||
app.kubernetes.io/instance: webapp
|
||||
fieldSpecs:
|
||||
- path: metadata/labels
|
||||
create: true
|
||||
@@ -1,4 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Namespace
|
||||
metadata:
|
||||
name: dev
|
||||
@@ -1,11 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
namespace: production
|
||||
resources:
|
||||
- ../../bases/backend
|
||||
- ../../bases/frontend
|
||||
- ../../bases/cache
|
||||
- ../../bases/database
|
||||
- namespace.yaml
|
||||
transformers:
|
||||
- labels.yaml
|
||||
@@ -1,10 +0,0 @@
|
||||
apiVersion: builtin
|
||||
kind: LabelTransformer
|
||||
metadata:
|
||||
name: labels
|
||||
labels:
|
||||
app.kubernetes.io/environment: production
|
||||
app.kubernetes.io/instance: webapp
|
||||
fieldSpecs:
|
||||
- path: metadata/labels
|
||||
create: true
|
||||
@@ -1,4 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Namespace
|
||||
metadata:
|
||||
name: production
|
||||
@@ -1,11 +0,0 @@
|
||||
apiVersion: kustomize.config.k8s.io/v1beta1
|
||||
kind: Kustomization
|
||||
namespace: staging
|
||||
resources:
|
||||
- ../../bases/backend
|
||||
- ../../bases/frontend
|
||||
- ../../bases/cache
|
||||
- ../../bases/database
|
||||
- namespace.yaml
|
||||
transformers:
|
||||
- labels.yaml
|
||||
@@ -1,10 +0,0 @@
|
||||
apiVersion: builtin
|
||||
kind: LabelTransformer
|
||||
metadata:
|
||||
name: labels
|
||||
labels:
|
||||
app.kubernetes.io/environment: staging
|
||||
app.kubernetes.io/instance: webapp
|
||||
fieldSpecs:
|
||||
- path: metadata/labels
|
||||
create: true
|
||||
@@ -1,4 +0,0 @@
|
||||
apiVersion: v1
|
||||
kind: Namespace
|
||||
metadata:
|
||||
name: staging
|
||||
@@ -1,74 +0,0 @@
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: backend
|
||||
namespace: secure
|
||||
spec:
|
||||
minReadySeconds: 3
|
||||
revisionHistoryLimit: 5
|
||||
progressDeadlineSeconds: 60
|
||||
strategy:
|
||||
rollingUpdate:
|
||||
maxUnavailable: 0
|
||||
type: RollingUpdate
|
||||
selector:
|
||||
matchLabels:
|
||||
app: backend
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: "9797"
|
||||
labels:
|
||||
app: backend
|
||||
spec:
|
||||
serviceAccountName: secure
|
||||
containers:
|
||||
- name: backend
|
||||
image: ghcr.io/stefanprodan/podinfo:5.0.3
|
||||
imagePullPolicy: IfNotPresent
|
||||
ports:
|
||||
- name: http
|
||||
containerPort: 9898
|
||||
protocol: TCP
|
||||
- name: http-metrics
|
||||
containerPort: 9797
|
||||
protocol: TCP
|
||||
- name: grpc
|
||||
containerPort: 9999
|
||||
protocol: TCP
|
||||
command:
|
||||
- ./podinfo
|
||||
- --port=9898
|
||||
- --port-metrics=9797
|
||||
- --grpc-port=9999
|
||||
- --grpc-service-name=backend
|
||||
- --level=info
|
||||
env:
|
||||
- name: PODINFO_UI_COLOR
|
||||
value: "#34577c"
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/healthz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- podcli
|
||||
- check
|
||||
- http
|
||||
- localhost:9898/readyz
|
||||
initialDelaySeconds: 5
|
||||
timeoutSeconds: 5
|
||||
resources:
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 512Mi
|
||||
requests:
|
||||
cpu: 100m
|
||||
memory: 32Mi
|
||||
@@ -1,19 +0,0 @@
|
||||
apiVersion: autoscaling/v2
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
name: backend
|
||||
namespace: secure
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: backend
|
||||
minReplicas: 1
|
||||
maxReplicas: 2
|
||||
metrics:
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: 99
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user